Transcription
TCP/IP FundamentalsEdmund LamIT Audit ManagerUniversity of Californiaedmund.lam@ucop.edu7/25/991
What we will discuss: TCP/IP related toOSI LayersHistory of TCP/IPand what is it?TCP/IP StructureIP Address StructureIP AddressNumbering7/25/99 IP AddressSubnettingIP RoutingTwo Types ofRoutersIP SecurityConcernsIPv6 High LevelDiscussion2
What we will not Discuss: Auditing of TCP/IPNetwork VulnerabilityInternet SecurityNetwork Troubleshooting7/25/993
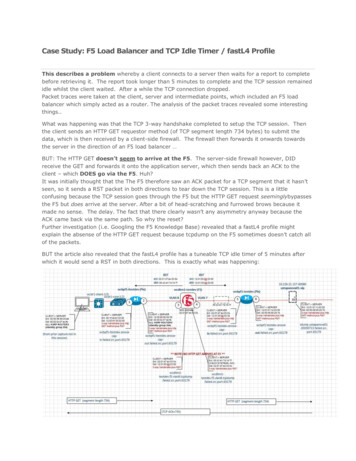
W orksta tionW orksta tionW orksta tionW orksta tionW orksta tionM ail S erverW orksta tionW orksta tionW orksta tionM ail S erverS erverS erverF irew allF irew allF irew allP roxyS erverE m ail, through P ort 25 ofP roxy S erver, is pa ssedthrough through the F irew allinto the E m ail S erve r7/25/99P roxyS erverIntern et4
Open Systems Interconnections(OSI)Reference Model Physical Layer - Physical Connections betweenComputers and the network. Converts bits intovoltages or light pulse. This defines topology(Connected through repeaters)Data Link -- Defines Protocol that Computers mustfollow. Token Ring, Ethernet (Connected withBridges)Network Layer -- Defines how the small packets ofdata are routed and relayed. (Connected withRouters)7/25/995
Open Systems Interconnections(OSI)Reference Model (Cont’d) Transport -- Defines how to address the physicallocations/devices on the network.Presentation -- Defines how applications can enterthe network. This layers allows devices to bereferenced as name rather than addresses.Application -- Interfaces with users, gets informationfrom databases, and transfer whole files. (Connectedthrough Gateways)7/25/996
Open System InterconnectionsReference Model:A p p lic a tio n(A d v is e )A p p lic a tio n(A d v is e )P re s e n ta tio n(P e rs o n )P re s e n ta tio n(P e rs o n )S e s s io n(S a le s )S e s s io n(S a le s )T ra n s p o rt(T ru s t)T ra n s p o rt(T ru s t)O S I L a ye rs7/25/99N e tw o rk(N o t)N e tw o rk(N o t)D a ta L in k(D o )D a ta L in k(D o )P h y s ic a l(P le a s e )P h y s ic a l(P le a s e )7
Connectors: 7/25/99Physical -- 4 pairs, Fiber Optics, Coax, NetworkInterface CardDatalink -- Token Ring, EthernetNetwork -- IPX, IPTransport -- TCP, UDP, NetBEUI, SPXSession -- FTP, Telnet, NCPPresentation -- SMB, NCPApplications -- Email, Appletalk, NFS8
E m ail Application(A dvise)E m ail Application(A dvise)A pplicationInteroperationF unctionsL o ca lC o n n e ctivityP resentation(P erson)P resentation(P erson)S ession(S ales)S ession(S ales)T ransport(T rust)T ransport(T rust)Internet workC onnectivityO S I LayersN etw ork(N ot)N etw ork(N ot)D ata Link(D o)D ata Link(D o)P hysical(P lease)P hysical(P lease)Local N etworkC onnectivity7/25/999
plicationWindows TransportTDI InterfaceTransportNetworkData LinkPhysical7/25/99TCPEthernetFDDIUDPIPNDIS InterfaceNIC Drivers PPPNetworkFrame RelayAdapterInternetNetworkInterface10
7/25/9911
Three Services that are important: DNS -- Domain Name Server (This server providesthe translation between IP address and DomainName e.g. www.abc.com to 121.11.131.11)WINS -- Windows Internet Name Service (Microsoftonly device to resolve name resolution)DHCP -- Dynamic Host Configuration Protocol(Aservice that enables the assignment of dynamicTCP/IP network addresses, based on a specifiedpool of available addresses)7/25/9912
TCP/IPDefinition:An industry standard suite ofprotocols providing communicationin a heterogeneous environment. Itprovides a routable, enterprisenetworking protocol and access tothe Internet and its resources7/25/9913
TCP/IP History DOE commissioned APANET in 1969First Telnet specification(RFC 318) in 1972File Transfer Protocol(FTP-RFC 454)introduced in1973TCP specified in 1974IP standard(RFC -791) published 1981Defense Communications Agencies establishedTCP/IP as a suite in 1982Domain Name System (DNS) introduced in 19847/25/9914
TCP (Transmission Control Protocol) Connection - oriented– Session is established before exchangingdata Reliable Delivery– Sequence numbers– Acknowledgements(ACKs) Byte-Stream CommunicationsUses Port Numbers as Endpoints toCommunicate7/25/9915
Some of the Well Know TCP Ports:A TCP port provides a specific location for delivery of TCPSegments. Port Numbers below 1024 are well-known, and areassigned by Internet Assigned Numbers Authority (IANA) – Refer toRFC 1170.TCP Port Number2021232580139DescriptionFTP (Data Channel)FTP (Control Channel)TelnetEmailHyperText TransferProtocol(HTTP) used for the WWWNetBIOS Session Service7/25/9916
TCP Packet Structure:TCP Source Port - Port of sending host.Destination Port – Port of End Point Destination.Sequence #. – Sequence of Bytes transmitted in asegment, required to verify all bytes are received.Acknowledgment Number – The sequence number of thebyte the local host expects to receive next.Data Length – Length of the TCP Segment.Reserved for Future Use.Flags – Specified what content is in the segment.Window – How much space is currently available in theTCP window.Checksum – Verify that the Header is not corrupted.Urgent Pointer – When urgent data is being sent.7/25/9917
IP Packet Structure Source IP AddressDestination IP AddressProtocol (Whether to pass up to TCP or UCP)Checksum (Verify that the packet arrivesintact)Time to Live(TTL) (Designates the number ofsecond the datagram is allowed to stay in thenetwork before it is discarded -- NT defaultsat 128 Seconds7/25/9918
Who has a UNIQUE IP addresses:Each Server, workstation,printer, router and otherInternet enabled devices7/25/9919
IP FormatNetwork IDHost IDEach IP address is a 32 bits long, and is composed of 4 8-bit fields, calledOctets. Each Octet represents a decimal number in the range of 0-255. Thisformat is called dotted decimal notation.E.g. Binary number as follow:10000011.01101011.00000011.00011000Dotted Decimal notation:131.107.3.247/25/9920
Converting IP Address from Binary toDecimal111111111286432168421Binary 110011111101111111111111117/25/99Bit Values012 14 2 18 4 2 116 8 4 2 132 16 8 4 2 164 32 16 8 4 2 1128 64 32 16 4 2 1Decimal Value013715316312725521
Address Classes:Network IDHost ID0Class A AddressRange 0 – 127.X.X.XN.H.H.HNetwork IDHost ID1 0Class B AddressRange 128 – 191.X.X.XN. N.H.HNetwork IDHost ID1 1 0Class C Address7/25/99Range 192 – 233.X.X.XN.N.N.H22
Possible Values for Each ClassClass AClass BClass CNumber ofNetworks12616,3842,097,152Number of Hostsper Network16,777,21465,534254Range of Network Ids(First Octet)1 –126(Note 1)128-191(Note 2)192 – 223 (Note 3)Note 1 – First Digit in first Octet is a “0”, and 127 is reserved for Loopbackfunction.Note 2 – First two Digits in first Octet are “10”.Note 3 – First three Digits in the first Octet are “110”7/25/9923
Other IP Address Rules: Net ID cannot be 127Net ID and Host ID cannot be 255(Allbits set to 1), it is reserved for broadcast– I.e. cannot be 255.255.255.1 Network ID and Host ID cannot be 0 (Allbits set to 0), it means “local networkonly”– I.e. cannot be 0.0.0.0 Host ID Must be unique to the Network– I.e. cannot have two networks on the samephysical wire7/25/9924
Typical Network IP Numbering101.23.145.9101.23.145.4W o rksta tio n W o rksta tio n L a p to p101.23.145.2c o m p u te r101.23.145.1IN TE R N E TS erve r101.23.145.23W o rksta tio R67.107.03.1W o rksta tio n W o rksta tio n L a p to pS erve r67.107.03.127/25/99c o m p u te rW o rksta tio n67.107.03.1425
Subnet Mask: A 32 bit address used to:– Block out a portion of the IP address todistinguish the network ID from the host ID– Specify whether the destination host’s IPaddress is located on a local or remotenetwork7/25/9926
Default Subnet Mask:AddressClassClass AClass BClass C 000000 0000000000000000 0000000011111111 255.0.0.0255.255.0.0255.255.255.0Using a Class B Subnet Mask:–––– Bits Used for Subnet MaskIP Address:045.121.16.23Subnet Mask: 255.255.0.0Network ID: 045.121.x.x/16Host ID:x.x.16.23/16All bits that corresponds to the Net ID are 1sAll bits that corresponds to the Host ID are 0s7/25/9927
Determining the Network IP Address: Use the logic of the AND Gate to calculate thefinal result to identify the Net ID– I.e. 1 and 1 is a 1–1 and 0 is a 0–0 and 0 is a 0 Network ID -- 045.121.x.x/16Host ID - 045.121.16.23/167/25/9928
Why Subnet? As Class A, B, and C IP Addresses are not available,this allows a business/organization to separatenetworks into different sub-networks as it growsOvercome limitations of current technologies, such asexceeding the maximum number of hosts persegmentsReduce network congestion as traffic grows within oroutside business/organizations.7/25/9929
Subnetting Process: Determine the number of Required NetworkIdsDetermine the number of Required Host Idsper SubnetDefine One Subnet Mask Based onRequirementsDefine a Unique Subnet ID for Each PhysicalSegment Based on the Subnet MaskDefine Valid Hosts Ids for Each SubnetBased on the Subnet ID7/25/9930
Determine the Number ofNetworks One for each subnetOne for each wide-area networkconnectionsSubnetting allows NetworkAdministrator to set up more networksthan the number of Class A/B/C IPaddresses allows.7/25/9931
Determines the Number of Host Idsper Subnet One required for each TCP/IP hostOne required for each router interfaceBy limiting the number of Hosts ID oneach subnet -- especially for smallernetworks, the Network Administratorcan implement more networks within theorganizations to enhance traffic flow7/25/9932
How Subnet Mask Work?Network IDSubnet IDHost IDFor a normal Class B AddressNumber of Network – 1Number of Subnets – 255 (0 – 254)Total number of Hosts – 65280 (255 Subnets X 256/Subnet)7/25/9933
Defining Subnet Mask from a PartialOctetNetwork IDSubnetIDHostIDHost IDFor a normal Class B AddressSubnet Mask : 255.255.248.0 or/21 (2 7 2 6 2 5 2 4 2 3 248)Number of Network – 1Number of Subnets – 32 (2 4 2 3 2 2 2 1 1)All Zeros and All Ones cannot be used as a Subnet or Host IDsTotal number of Hosts – 65472 (32 Subnets X 2046/Subnet)7/25/9934
Subnet Conversion Tables:(Class A)Number ofSubnets026143062126254No. ofRequired Bits12345678Subnet 8.0.0255.252.0.0255.254.0.0255.255.0.0Number ofHosts 262,142131,07065,534Class A Subnet Using One Octet7/25/9935
Subnet Conversion Tables:(Class B)Number ofSubnets026143062126254No. ofRequired Bits12345678Subnet .0Number ofHosts ass B Subnet Using One Octet7/25/9936
Subnet Conversion Tables:(Class C)Number ofSubnets026143062126254No. ofRequiredBits12345678Subnet 4255.255.255.255Number ofHosts perSubnetInvalid62301462InvalidInvalidClass C Subnet Using One Octet7/25/9937
Another Way to Define No. ofSubnet Ids: Formula:– No. of Subnet available with “n” bits youare using for subnetting 2 n -2Example:– We are using three digits from Octet tocalculate the number of subnets:– 2 3 - 2 8-2 6 subnets possible7/25/9938
From a Subnet Mask and NetID Assume a Class B Address:– 121.045.X.X Using Subnet Mask of:– 11111111.11111111.11110000.00000000 We will come up with a list of SubnetIds, using matrix in Slide 36, on Slide38.7/25/9939
Defining Subnet ID(Class B with 4 used for Subnet in 3rd Octet)2 700000000111111117/25/992 600001111000011112 500110011001100112 401010101010101012 300000000000000002 200000000000000002 100000000000000002 00000000000000000 0 (Not Valid) 16 32 48 64 80 96 112 128 144 160 176 192 208 224 240 (Not Valid)40
Subnet ID Identification(Class B with 4 used for Subnet in 3rd Octet)Subnet OctalDecimal Value 0 (Not Valid) 16 32 48 64 80 96 112 128 144 160 176 192 208 224 240 (Not Valid)7/25/99Net X121.045.208.X121.045.224.X Subnet ID is notconsecutivelynumbered.Only 14 could beidentified with 4 bitsused in third Octetfor Subnetting41
Defining Host ID for a Subnet:Octet 0000110000001101000011100000111100007/25/99Subnet Octet Beginning RangeDecimal ValueValue0(Not X.208.1224X.X.224.1240(Not Valid)InvalidEnding 3.254X.X.239.254Invalid42
Subnetting: Allows Network Administratorsovercome the physical limitations ofnetwork’s capacity.Allows an effective increase in networkbandwidth, by cutting down on theamount of broadcasts a network mustprocess.7/25/9943
Subnetting does not provide: An easy way to classify the Host toeasily be identified in a certain subnetworkEasy calculations to identify where ahost is– Requires network diagrams to troubleshootnetwork problems7/25/9944
What is IP Routing? Routing is the process of choosing apath over which to send packetsThis occurs when a TCP/IP host sendsIP packets and routing occurs at an IProuter.Notice the difference amongrepeater,bridge, and routers -- refer toDefinitions7/25/9945
How Does Router Work? Communicating IP Hosts determineswhether the communicated host is onlocal or remote network– Local -- same network/sub-network– Remote -- Outside Local network If Remote, Host checks router IP routingTable for a route to send through whichport. Host and Network address mustbe specific7/25/9946
Typical Network IP Numbering101.23.145.9101.23.145.4W o rksta tio n W o rksta tio n L a p to p101.23.145.2c o m p u te r101.23.145.1IN TE R N E TS erve r101.23.145.23W o rksta tio R67.107.03.1W o rksta tio n W o rksta tio n L a p to pS erve r67.107.03.127/25/99c o m p u te rW o rksta tio n67.107.03.1447
How Does Router Work? If no IP address and port is found, itsends to a default gateway address.The Routing Table in the defaultgateway is then consulted, and thisprocess continues for a determinednumber of times before the packet isreturned if the IP is not found.7/25/9948
Two Types of Routers: Static Routing -- Function of IP– Routers do not share routing information– Routing tables are built manually Dynamic Routing -- Function of InterRouting Protocols– Routers share routing informationautomatically– Requires routing protocol, e.g RIP orOSPF.7/25/9949
Static IP Routing: The router only communicates withnetworks with a configured interfaceIt does not send new configurationdownstream– Excellent for Firewall and high securityenvironment7/25/9950
Static IP Routing Typical Arrangements:1 01 .2 3 .14 5 .91 01 .2 3 .14 5 .4W orkstation W orkstation1 01 .2 3 .14 5 .2L aptop c om pu ter101.23.145.1IN T E R N E TS e rv e r1 01 .2 3 .14 5 .23W orkstationRO UTER A1 01 .2 3 .14 5 .25103.121.73.2103.121.73.XN e xtw o rk X103.121.73.4Firew all67.107.04.1RO UTER CTypical S taticR outingN etw ork67.107.03.16 7.1 0 7 .03 .16 7.1 0 7 .03 .46 7.1 0 7 .03 .5W orkstation W orkstationS e rv e r6 7.1 0 7 .03 .12L aptop c om pu terW orkstation6 7.1 0 7 .03 .14N e xtw o rk Y7/25/9951
How It Works: Router A has only local connection toNetwork X and Firewall Router. Hostson Network X cannot directlycommunicate with Hosts on Network Ywithout going through the FirewallRouter. Same for Host in Network YTo route IP packets to other networks:– Each address must be manually enteredonto the Routing Table to route IP packets– A default gateway address to anotherrouter’s local interface is required527/25/99
Typical Routing Table:Routing Table for Router 1.73.253
Dynamic IP Routing: Using RIP protocol, routersautomatically exchange routes to knownnetworks with each other, and updateany changesNormally installed on large intranetworksOnly need to set the default gatewayaddress to match the IP address of thelocal router’s interface7/25/9954
TCP/IP Security Concerns IP Addresses can be spoofed -snooped and replacedSyn Flood AttackSpamming through incorrect IPaddressesDenial of Service Attack7/25/9955
Packet Filtering Firewall Packet Filtering– Using Routers, and packet filtering rules togrant or deny access.– Source and Destination Addresses in theIP packet header can be spoofed.– Do not protect against IP or DMS addressSpoofing.– Does not support logging or userauthentication.– Attackers will have direct access to hostonce they pass through firewalls.7/25/9956
Application Gateways Firewall: The Proxy Server Program examines externalrequest, and forward legitimate ones tointernal hosts to provide requested services– Considered most secured Firewall.– Gateway can be configured as the onlyexternal IP address.– Prevent Direct Access to servers andservices.– Strong User Authentication and detailedLogging.– Requires a proxy for each service.7/25/9957
Hybrid or Complex Gateway: Combination of Packet Filtering and Proxy ServerGateway.– In Parallel -- will only secure the least secure of bothmethods.– In Series -- the overall security is enhanced.7/25/9958
Firewall Architectures: Multi-homed:– A host(firewall) that has more than onenetwork interface, each connected to aseparate physical network.– Dual homed (2-NIC cards - One facingExternal, the other facing Internal)7/25/9959
Firewall Architecture: (Cont’d) Screened Host:– Use a Bastion Host to filter all externalrequests prior to routing, e.g. using packetfiltering. These hosts are normally set atthe outside of the internal network.7/25/9960
Screened Subnet Firewall: Same as Screened Host, however,extra security is added by creating anetwork which the bastion host resides.They are separate from internalnetwork.7/25/9961
Strength and Weakness of Firewalls: ( 7/25/99 % " " ! ! ! !! ! " # !! " % ! & ' ) " * ! " ' ! ! ) , ) ) !! 62
Overview of IPv6 IP Version 1 - 3 were not formallyassignedIP Version 4 - TCP/IP -- 32 bit IP address,currently usedIP Version 5 -- Streamed Protocol(ST), aconnection-oriented internet-level protocolIP Version 6 -- Designed to Replace IPv4 - 128 bit IP address.7/25/9963
IPv6 has following Advantages: Essentially Unlimited Addresses– 296 times more than the number of IPv4addresses Simplified auto-configuration: IPaddresses are generated whenhardware is plugged into networkIPv6 header is designed for optimizedprocessed7/25/9964
IPv6 has following Advantages:(Cont’d) Must implement standardized set ofsecurity features– Authentication Header– Encapsulating Security Payload(ESP)service Native multicast supportSupport to automatically renumberentire networks7/25/9965
IPv6 Security: IPv6 Authentication Header givesnetwork applications a guarantee that apacket did come from an authenticatedsourceESP encrypts the IP datagram so thatthe information will not be visible tosnoopers7/25/9966
IPv4 Header4 for IPv41 byteVERSHL1 byte1 byteService1 byteFragment LengthDatagram IDFLAG Fragment OffsetTTLProtocolHeader ChecksumSource AddressDestination AddressOptions (if any)Data7/25/9967
6 for IPv61 byteIPv6 Header1 byteVERS PRIOPayload Length1 byte1 byteFlow LabelNext HeaderHop LimitSource Address (128 bits - 16 bytes)Dest. Address (128 bits - 16 bytes)7/25/9968
IPv6 Header Fields VERS: 6 (IP version number) Priority: will be used in congestion control Flow Label: experimental - sender canlabel a sequence of packets as being inthe same flow. Payload Length: number of bytes ineverything following the 40 byte header, or0 for a Jumbogram.7/25/9969
IPv6 Header Fields Next Header is similar to the IPv4“protocol” field - indicates what type ofheader follows the IPv6 header. Hop Limit is similar to the IPv4 TTL field(but now it really means hops, not time).7/25/9970
IPv6 Addresses 128 bits - written as eight 16-bit hexnumbers.5f1b:df00:ce3e:e200:0020:0800:2078:e3e3 High order bits determine the type ofaddress. The book shows thebreakdown of address types.7/25/9971
IPv6Aggregate Global Unicast Address313001 TLA ID321664NLA IDSLA IDInterface IDTLA: top-level aggregationNLA: next-levelSLA: site-levelInterface ID is based on hardware MAC address7/25/9972
IPv4-Mapped IPv6 Address IPv4-Mapped addresses allow a hostthat support both IPv4 and IPv6 tocommunicate with a host that supportsonly IPv4.The IPv6 address is based completelyon the IPv4 address.7/25/9973
IPv4-Mapped IPv6 Address 80 bits of 0s followed by 16 bits of ones,followed by a 32 bit IPv4 Address:7/25/990000 . . . 0000FFFFIPv4 Address80 bits16 bits32 bits74
IPv4-Compatible IPv6 Address An IPv4 compatible address allows ahost supporting IPv6 to talk IPv6 even ifthe local router(s) don’t talk IPv6.IPv4 compatible addresses tell endpointsoftware to create a tunnel byencapsulating the IPv6 packet in anIPv4 packet.7/25/9975
Definitions: Appletalk -- A dedicated protocol for Apple networkIPX/SPX -- Basic Protocol used on a NetwarenetworkNFS -- Network File System -- A UNIX dedicatedprotocolSMB, NCP -- Server Message Block, Netware CoreProtocol, they are redirectors protocols to interceptrequests, format them according to protocol in use,and pass the messages to lower levelNetBUEI -- NetBios Extended User Interface, a nonroutable protocol used in smaller networks7/25/9976
Definitions (Cont’d) UDP -- User Datagram Protocol, a connectionlessprotocol that sends packets to different computers orsystemsTDI -- Transport Driver Interface (Lets applicationprogrammers create components for Session layer tocommunicate down to Transport Layer)NDIS -- Network Device Interface Specification(AnApplication Program Interface designed to facilitatecommunication between transport protocol driversand the underlying network interface drivers. Itprovides the ability to use more than one protocolover a single network card)7/25/9977
Definitions (Cont’d) FDDI -- Fiber Distributed Data Interface (Very fastand expensive fiber network access method -- Up to100Mbps)PPP -- Point to Point protocol (A communicationprotocol that provides dial-up access to a network,normally used to connect to Internet)Frame Relay -- A point to point networkcommunications media that moves packets withoutstripping any information on the packets.NetBIOS -- The main protocol used by Windows NT7/25/9978
Definitions (Cont’d) Router -- A router is a device that forwardsthe packets from one physical network toanother -- normally known as a gateway.Routers are connected at Network LayerA Bridge -- A device that joins two LANs. Itallows stations on either network to accessresources on the other. Bridges areconnected at the Data Link LayerRepeater -- A device that regenerates signalsso they can travel on additional cable length.Repeaters connected at Physical Layer7/25/9979
Definitions (Cont’d) RIP -- Routing Information Protocol, aprotocol that enables communicationbetween routers on a network to facilitate theexchange of routing tables.OSPF -- Open Shortest Path First, a link staterouting algorithm. This allows routers torespond quickly to changes in network, anduses the Dijkstra algorithm to calculate theroutes based on no. of hops, line speed,traffic, and cost.7/25/9980
References for this Presentation: Networking Essentials - Microsoft PressInternetworking with TCP/IP in MS Windows NT 4.0 Microsoft EducationPractical UNIX & Internet Security -- O’Reilly AssociatesWindows NT Server - Introduction to TCP/IP WhitePaper -- MicrosoftExam CRAM - TCP/IP -- Certification Insider PressHandbook of Information Security Management -1999 -- Auerbach PressRFC 2373 -- IPv6 Addressing Architecture (7/1998)7/25/9981
networking protocol and access to the Internet and its resources. 7/25/99 14 TCP/IP History DOE commissioned APANET in 1969 First Telnet specification(RFC 318) in 1972 File Transfer Protocol(FTP-RFC 454)introduced in 1973 TCP specified in 1974 IP standard(RFC -791) published 1981