Transcription
EUROCONTROLATM Cybersecurity Maturity ModelLevel 1Edition: 1.0Edition date: October 2017Status: ReleasedIntended for: General PublicFOUNDINGMEMBERSUPPORTING EUROPEAN AVIATIONNETWORKMANAGER
ATM Cybersecurity Maturity Model – Level 1DOCUMENT APPROVALThe following table identifies all management authorities who have successively approvedthe present issue of this document.AUTHORITYNAME AND SIGNATUREHead of SQS UnitDr. Frederic LieutaudHead of Safety Unit,DNM, NOMMr. Antonio LicuHead of Network OperationsManagement DivisionMr. Kenneth ThomasDirector NMMr. Joe SultanaEdition: 1.0Page 2DATE
ATM Cybersecurity Maturity Model – Level 1DOCUMENT CHANGE RECORDThe following table records the complete history of the successive editions of the presentdocument.EDITIONNUMBEREDITIONDATE0.1REASON FOR CHANGEPAGESAFFECTED30/06/2018Creation of the Working DraftAll0.223/08/2019Draft version after 22 Aug 2018 Workshopwith ANSPs and NMAll22/09/2018Incorporating the comments after initialtrials and in prep for the WS on 5th of Novwith ANSPs and NMAll0.30.422/10/2018Version post Workshop on 5th of NovAllAll0.510/01/2019Version in advance of 14 Feb 2019 WSwith ANSPs and NM and incorporating allthe feed-back from application with NM top10 suppliers and ANSP trial of the model0.615/02/2019Proposed Issue after WS on 14th FebAll1.020/02/2019Released issueEdition: 1.0INFOCENTREREFERENCEPage 3
ATM Cybersecurity Maturity Model – Level 1CONTENTSDOCUMENT APPROVAL . 2DOCUMENT CHANGE RECORD. 3CONTENTS . 4Introduction . 5High-level model. 10Scoring form . 14Detailed model . 16Abbreviations . 19Acknowledgements. 20Edition: 1.0Page 4
ATM Cybersecurity Maturity Model – Level 1IntroductionWhat is a cybersecurity maturitymodel?A cybersecurity maturity model describes a range of capabilities that you would expect to see in an organisation withan effective approach to cybersecurity. Each capability will have a description of the kinds of activities and processesyou would expect to see, at different levels of maturity. An organisation assessing its overall cybersecurity maturitycompares its own practices against those described in the levels of each capability, backing up the assessment withsome evidence to justify the result.Maturity models are a highly simplified (but still useful) view of reality. They are not the same as a detailed audit, gapanalysis and/or review, which still serve crucial purposes in cybersecurity.Who is the model for?The model is for Chief Information Security Officer (CISO) and/or cybersecurity managers (and similar roles) to use.Given the simplicity of the results, and focus on the most critical elements, the audience of the maturity is most likelyto be top management.How has the model been created?EUROCONTROL’s Network Manager (NM) commissioned a review by Helios, partnering with Prof Chris Johnson, toundertake a review of the cybersecurity of the NM and its critical suppliers. A maturity model approach was taken tobe able to compare the suppliers. Publishing the maturity model for wider use is one of the review’s goals. The initialmodel was developed after an August 2018 workshop with the NM and various Air Navigation Service Providers(ANSPs). The workshop identified critical areas and generated ideas that were then consolidated into a model to beroad-tested with NM suppliers and revised as a result. Further updates are expected to refine the model over time(e.g. to automate reporting and to link the capabilities to a control type – i.e. People/Process/Technology - so that itcan highlight where the organisation is strong and weak, and this can help drive additional investment).Why create an ATM cybersecuritymaturity model?Being developed by the NM and ANSPs, and being used in the Air Traffic Management (ATM) industry, the model hasmost immediate applicability to ATM. Whilst not being designed for wider application, it may be useful. The potentialusefulness of a model had been expressed by some ANSPs, and this model combines the elements that are mostrelevant to ATM today. In reality, this is a mixture and tailoring of various wider standards and guidelines. Note thatthe model does not identify new requirements for ATM stakeholders – instead it is capability and process-based,leaving detailed requirements to each organisation. Another advantage of using the model is that it gives a snapshotthat brings together much information that may not otherwise be in a single document.
ATM Cybersecurity Maturity Model – Level 1Is the model based on a standard?How can the model be used?How many maturity levels are there?Does my organisation need to be atthe highest level of cyber-maturity?How do I use the model?Yes, the model is founded on NIST’s Cyber Security Framework (CSF), together with some elements of ISO 27001. NISTCSF was chosen as a pragmatic and well-used standard. The ‘Tiers’ within the CSF were a helpful starting point, andlinked (crucially) to a wider target-setting process that encompasses an organisation’s business objectives, threat/riskenvironment, and requirements and controls. The CSF was extended to emphasise the leadership and governance,drawing on ISO 27001. The role of human factors in security has also been emphasised. The purpose of the model is tohighlight the most critical elements in the ATM context. It is not a replacement for applying the whole standard. Tomaintain traceability with the NIST CSF, the highlighted text denotes new/modified text with respect to the NIST CSFAs a common reference in the ATM industry, four use cases are foreseen:1. Comparing your organisation to how it looked in the past, to track improvements over time2. Comparing your organisation to how it should look in the future after a roadmap of improvements is completed3. Comparing your organisation’s practices with others to develop and share good practice4. Assessing suppliers and supply chain maturityThere are five maturity levels defined, ranging from ‘Non-existent’ to ‘Adaptive’. These are inspired by the ‘Tier’terminology from the NIST CSF.No. The model allows a broad assessment of strengths and weaknesses. Crucially it should facilitate discussions overimprovement areas and the practices required to improve maturity. However, the overall goal is unlikely to be thehighest level of maturity on all scores as each organisation’s target is different, depending on threats, budget, etc.The model has two levels of detail. Use of the high-level model is described here. It be undertaken independently ofthe more detailed model. The more detailed model is described later.The high-level model is a really simple maturity assessment with 13 capabilities and a classic maturity model answerset, indicating what Level 3 means, and what Level 4 means, etc. This enables assessment in under an hour bysomeone who has a suitably broad overview of that organisation. Given the broad and holistic nature of the maturitymodel, assessments from a range of perspectives, including from technical and operational personnel, will often beneeded. Discussion and insight arising from any differences in perspective are a benefit of the assessment.The selected capabilities are the ones that are seen as most important and relevant. A form is provided to complete,including rationale and evidence. Your organisation must fulfil all elements of one level before you can say you are atnext level; i.e. if you are any missing earlier elements then you must assess yourself at the lowest level that you fulfilall elements. Each capability also has a set of ‘probing questions’ that can be used to challenge the organisationthrough more open questioning.Application to a supplier can be done by the supplier itself, or by the customer or a third party.The model can, of course, be adapted as required for your organisation. In that sense, it simply offers a potentialframework to use.
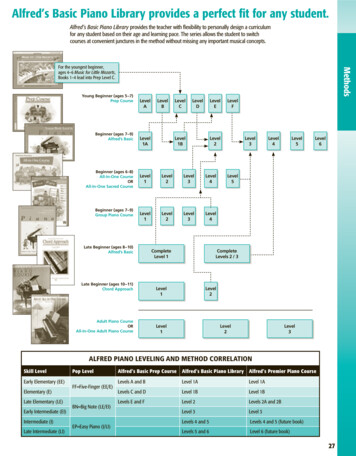
ATM Cybersecurity Maturity Model – Level 1What is the output?The following is an example of how the results can be presented to top management. Here there is an assessment ofthe ANSP and five of its suppliers. The suppliers have been ordered from most mature to least r5333211Cyber Security Management System (CyberSecMS)232221Asset Management443221Risk Assessment133121Information sharing232110Supply Chain Risk Management233210Identity Management and Access Control342232Human-centred security133220Protective Technology342311Anomalies and Events322220Response Planning233300Mitigation332201Recovery Planning333121FunctionCategoryLEAD ANDGOVERNLeadership and governanceIDENTIFYPROTECTDETECTRESPONDRECOVERANSP
ATM Cybersecurity Maturity Model – Level 1What should I do after using themodel?The model should give a broad assessment of strengths and weaknesses, and specifically where there are gapsbetween current and target maturity. Improvements can be identified and placed into a roadmap to increase maturity.NIST CSF guidance on establishing and improving a security programme can be used and adapted (as in the figurebelow) if required. Specific metrics may be needed to track improvements in particular capabilities.
ATM Cybersecurity Maturity Model – Level 1What if I am already ISO27001certified?Congratulations. The maturity model is still intended to be helpful, even if your organisation’s Information SystemManagement System (ISMS) is fully compliant with ISO27001 requirements. If the operational environment (for anANSP) or product development or service delivery function (for suppliers) is part of the Statement of Applicability,there should be a broad correlation between ISO27001 compliance and maturity. The maturity model is then anadditional check on whether some key controls are appropriately strong and robust. Furthermore, note that whilst theterm Cybersecurity Management System (CyberSecMS) is used here, it is effectively equivalent to an ISMS, and part ofa broader Security Management System (SecMS).
ATM Cybersecurity Maturity Model – Level 1High-level modelMaturity om NIST)Top managementdemonstrate leadershipand commitment tocybersecurity. Thepolicies needed tomanage and monitorthe organisation’sregulatory, legal, risk,environmental, andoperationalrequirements areunderstood and informthe management ofcybersecurity risk.The organisation has aset of interactingelements thatestablishes securitypolicies and securityobjectives, andprocesses to achievethose objectives.The data, personnel,devices, systems, andfacilities that enable theorganisation to achievebusiness purposes areidentified and managedconsistent with theirrelative importance tobusiness objectives andthe organisation’s riskstrategy.The organisationunderstands thecybersecurity risk toorganisationaloperations (includingmission, functions,image, or reputation),organisational assets,and individuals,Level 0 - NonexistentLevel 1 – PartialLevel 2 – DefinedLevel 3 – AssuredLevel 4 – AdaptiveNo overarching policy,strategy or planPolicy established,together with parts of astrategy or plan; roles &responsibilities areestablished but no orweak link with topmanagementPolicy supported by astrategy and planapproved by topmanagement; key risksare accepted by topmanagementPlan is funded and, withvisible top managementcommitment, deliveringintended improvementsacross the organisationUpdated regularly toreflect progress, threatsand risksNo documentedCyberSecMSParts of a CyberSecMSdocumented, resourcedand applied, butindependently of otherdepts/systemsFully operationalCyberSecMS, that isexternally auditedCyberSecMS, and withlinks to other parts of theSecMS and the QMS andSMSCertified CyberSecMS,with KPIs defined andtracked, andCyberSecMS/QMS/SMSprocesses are coordinatedRegular review againstnew good practices; KPIsshow continualimprovement; CertifiedIntegrated ManagementSystem (IMS)Ad hoc, not formalisedAll critical systems andinterfaces are identifiedand described in aconsistent way with clearownersInterdependencies arewell-understood andthere is regular reviewand updatesAutomated updates asthe environment changesManagement-approvedprocesses that lead tocyber requirements beingidentifiedConsistent, organisationwide application withidentified risk andrequirement owners;external validation of risklevels by authorities;Security risk assessment istaken into account inContinual review andlinking of risks to latestvulnerabilities andthreats; assurance thatsystem-of-systemsaspects are addressedNo formal inventory ofsystems, theirinterdependencies andinterfacesNo documented riskassessment processes orassessmentsAd hoc; no formalisedassessment process
ATM Cybersecurity Maturity Model – Level 1including system-ofsystem aspectsresulting fromdependencies.IDENTIFYPROTECTsafety risk assessment,and vice versaNo, or very limited,cybersecurity informationsharingUsing some threatintelligence andvulnerability information;Informal informationsharing internally andexternally whereappropriateTrends are identified;Internal and externalsharing based on formalprocesses linked to riskassessment, vulnerabilitymanagement, responseand recovery processes;Relevant risk informationis shared between safetyand security functionsThreat intelligence andvulnerability informationfor all critical systems;Consistent, widespreadand effective sharingInformation sharing ishabitual and proactive;demonstrable leadershipin improving industrywide information sharingMinimum set ofrequirements placed onall critical suppliers andagreements withpartners, with mostly selfassessment forcomplianceRequirements placed onsuppliers withproportionate compliancechecks and processes /penalties / measures fornon-complianceIndependent reviews /audits / assessmentssupporting regularupdates of requirementsagainst new goodpracticesInformationsharingThe organisationobtains and sharesthreat intelligence,vulnerability andincident informationactivities, with internaland external partiesSupply ChainRiskManagementThe organisation’spriorities, constraints,risk tolerances, andassumptions areestablished and used tosupport risk decisionsassociated withmanaging supply chainrisk. The organisationhas in place theprocesses to identify,assess and managesupply chain risks.Appropriate levels oftrust are establishedwith data exchangepartners.No complete overview ofall suppliers / partnersSome requirementsplaced on some suppliersand agreements withsome partners; partialand informalunderstanding ofsupplier/partner cybermaturityIdentityManagementand AccessControlAccess to physical andlogical assets andassociated facilities islimited to authorisedusers, processes, anddevices, and is managedconsistent with theassessed risk ofunauthorised access.No access controls oncritical systems or areasAccess controls on somecritical systems and areasAccess controls on allsystems and areas andlinked to logsConsistent controls withinorganisation-wideapproach, includingsupply chainRegular updates againstnew good practicesHumanCentredSecurityThe organisation’spersonnel and partnersare providedcybersecurityawareness educationAd hoc activities to informand educateCoherent programme inplace that addresseswhole organisation,including addressinghuman factors andSustained activities withfollow-ups, differentiatedfor different roles, leadingto increasing complianceand performanceState of the art syllabus,with systematic testing,leading to routine andproactive cyber-riskreporting from staffNo awareness/trainingprogramme
ATM Cybersecurity Maturity Model – Level 1PROTECTProtectiveTechnologyDETECTorganisational culturePrimary reliance onnetwork boundaryprotection (‘castle wall’)Some requirements fortechnical controls aredefined upfront,supporting the ‘securityby-design’ principle; somenon-essential services aredisabledAnomaliesand EventsAnomalous activity isdetected in a timelymanner and thepotential impact ofevents is understood.ResponsePlanningResponse processes andprocedures areexecuted andmaintained, to ensuretimely response todetected cybersecurityevents.No plans exist to respondto security anomaliesPlans exist with high-levelresponsibilitiesMitigationActivities are performedto prevent expansion ofan event, mitigate itseffects, and eradicatethe incident.Incidents cannot becontained or mitigated;there is no gracefuldegradation of servicesSome incidents can becontained or mitigatedwithout full loss ofservices; in some casesfull loss of services cannotbe avoidedRESPONDRESPONDand are adequatelytrained to perform theirinformation securityrelated duties andresponsibilitiesconsistent with relatedpolicies, procedures,and agreements.Security is part of theorganisation’s culture.Technical securitysolutions are managedto ensure the securityand resilience ofsystems and assets,consistent with relatedpolicies, procedures,and agreements.Systems and processesare designed to besensitive to theadditional workloadcreated bycybersecurityrequirements.No documentedprocedures or controlsAd hoc and typicallymanuallyRequirements fortechnical controls aredefined andimplemented; theprinciple of leastfunctionality is alsoimplemented (e.g. nonessential services areturned off) on all criticalsystemsSuitably resourcedcontrols are in place todetect anomalies andevents; some detection isautomatic; penetrationtesting flags missedpositivesWell-definedresponsibilities at alllevels, 24/7/365 reactiontimes based on logic andagreements withsuppliers / partners;violations of plans areaddressedIncidents can becontained and/ormitigated with minimalservice loss; Sites haveappropriate manualdisaster recovery servicesTechnical controls aredemonstrated to beeffective; Securityarchitecture with virtualseparation implementedand effective; Full controlover technicalinfrastructure;Implementation designedwith the human in mind,making it ‘easy to do theright thing’ and ‘hard todo the wrong thing’Security architecture canadapt dynamically tochanging threat and risklandscapeProcedures to reducefalse positives; resourcingincludes safeguardsand/or emergency coverState of the art detectioncapabilities are combinedwith additionalmitigations when newthreats are known not tobe detectableExercises and audits driveimprovements in plans;resourcing includessafeguards and/oremergency cover;information sharingincludes voluntary sharingwith other partiesSites have automateddisaster recovery serviceswith limited (or no)human intervention; databreaches and loss of dataintegrity have well-Response planning iswidely coordinated,frequently exercised andupdated, drawing on newgood practices andknowledgeMitigations aremonitored, regularlytested and adapted toensure alignment withthe operationalenvironment; Automation
ATM Cybersecurity Maturity Model – Level 1RECOVERRecoveryPlanningRecovery processes andprocedures areexecuted andmaintained to ensuretimely restoration ofsystems or assetsaffected bycybersecurity events.No recovery proceduresestablished for cyberincidentsProcedures exist for somesystemsProcedures exist for allcritical systems, togetherwith backups for systemsand data to recover fromoutagesrehearsed mitigationsexists to address incidentsbefore they are apparentto humans; Self-healingexistsRegular testing ofprocedures, includingcommunication withinternal and externalstakeholdersLessons identified fromexercises and incidents(both internal andexternal) drive updates inpolicy and procedures
ATM Cybersecurity Maturity Model – Level 1Scoring cation?Justify the scoreEvidence?Provide evidence for thescoreAdditional probing questions aimed atANSPs Do you have an approved policy, strategy, planand budget? How is the whole organisation aligned withthem? Who is responsible for what? How do you ensure that security is integratedinto all operational processes? What standards(s) do you use? How is the CyberSecMScoordinated/integrated with the QMS/SMS? How do you measure the effectiveness of theCyberSecMS? How many critical systems / assets do youhave? How do you label physical and data assets? What are their dependencies? What is your patching policy? How do you identify and trace vulnerabilities?Additional probing questions aimed atATM suppliers Do you have an approved policy, strategy, planand budget for securing the product/service? How is the whole organisation aligned withthem? Who is responsible for what? How do you ensure that security is integratedinto all processes that deliver theproduct/service? What standards(s) do you use? If there is a supporting CyberSecMS, how is itcoordinated/integrated with the QMS/SMS? How do you measure the effectiveness of theCyberSecMS? How many critical systems / assets do youhave for delivering the product/service? How do you label physical and data assets? What are their dependencies? What is your patching policy? How do you identify and trace vulnerabilities? How do you identify and assess threats? Is there a process that identifies, assigns andtracks cyber requirements? How do you ensure that the process works? What is your risk tolerance your ownorganisation and your customers?RiskAssessment How do you identify and assess threats? Is there a process that identifies, assigns andtracks cyber requirements? How do you ensure that the process works? What is your organisation’s risk tolerance?Informationsharing Supply ChainRiskManagement How do you determine the level of trust youhave with different suppliers / partners? How do you ensure the right requirements areplaced on suppliers? How do you ensure the right supplier/partnerbehaviours? How do you determine the level of trust youhave with different sub-contractors / partners indelivering the product/service? How do you ensure the right requirements areplaced on sub-contractors? How do you ensure the right subcontractors/partner behaviours?IdentityManagementand AccessControl Who do you share risk information with?How do you assign access rights? Who do you share risk information with?How do you assign access rights?
ATM Cybersecurity Maturity Model – Level maliesand veryPlanning How do you ensure that awareness leads tothe right behaviours? What indicators do you use to predict who willlater be detected violating security policy? Do you have a defined security architecture(for now or future)? How does it support security by design? How does it support data exchange andprotection, and resilience? How have you addressed the human factors inensuring security controls are effective? How do you ensure that all cyber events /incidents can be detected? How do you determine the required reactiontimes for services? Do you consider cyber-attacks with subtle andbelievable data manipulation? Do you have a Service Level Agreement (SLA),or similar requirements, between Ops andsupporting departments (inc IT)? How you ensure that enough resourcing is inplace to respond to events/incidents? How do you respond to security events? Who do you communicate with during anincident (internally and externally)? How often are the lines of communicationtested? Are contacts named or are they roles andnumbers that automatically change as peoplemove roles in an organisation? Are the means of contact (phones, email, etc)themselves resilient to an attack? Do your operational contingency proceduresinclude cyber incidents? How do you return to normal operation? How do you ensure that awareness leads tothe right behaviours? What indicators do you use to predict who willlater be detected violating security policy? Do you have a defined security architecture(for now or future)? How does it support data exchange andprotection, and resilience? How do you ensure that all cyber events /incidents can be detected? How do you determine the required reactiontimes for services? Do you consider cyber-attacks with subtle andbelievable data manipulation? Do you have a Service Level Agreement (SLA),or similar requirements, between thedepartments that deliver the product/service? How you ensure that enough resourcing is inplace to respond to events/incidents? How do you respond to security events? Who do you communicate with during anincident (internally and externally)? How often are the lines of communicationtested? Are contacts named or are they roles andnumbers that automatically change as peoplemove roles in an organisation? Are the means of contact (phones, email, etc)themselves resilient to an attack? For services, do your contingency proceduresinclude cyber incidents? For services, how do you return to normaloperation?
ATM Cybersecurity Maturity Model – Level 1Detailed modelThere will also be a more detailed maturity assessment, breaking down each of the high-level capabilities into more detailed areas. The extra detail would come from theNIST CSF, along with its references for further guidance. Such a detailed model is also best applied recursively – i.e. by department, function or system level beforecombining (by averaging maturity levels) for an overall result. This approach will require much more extensive liaison with stakeholders (e.g. relevant ANSP departmentsinclude Ops, IT, equipment, procurement, safety, quality, etc).The excel version of the detailed questionnaire for Level 1 Maturity Model - has been appended to this report.
ATM Cybersecurity Maturity Model ‐ Level 1FunctionCategoryLevel (0‐4)LevelCommentsJustification?Justify the scoreEvidence?Provide evidence for the scoreDescription (mostly from NIST)Level 0 ‐ Non‐existentTop management demonstrateleadership and commitment tocybersecurity. The policies needed tomanage and monitor the organisation’sregulatory, legal, risk, environmental,and operational requirements areunderstood and inform the managementof cybersecurity risk.No overarching policy,strategy or planLevel 2 – DefinedLevel 3 – AssuredLevel 4 – AdaptivePolicy established, togetherPlan is funded and, with visiblePolicy supported by a strategytop managementwith parts of a strategy orand plan approved by topUpdated regularly to reflectcommitment, deliveringplan; roles & responsibilitiesmanagement; key risks areprogress, threats and risksintended improvementsare established but no or weakaccepted by top managementlink with top managementacross the organisationLeadership and governance4AdaptiveUpdated regularly toreflect progress, threatsand risksCybersecurity ManagementSystem (CyberSecMS)3AssuredCertified CyberSecMS, withKPIs defined and tracked,andCyberSecMS/QMS/SMSprocesses are coordinatedDefinedAll critical systems andinterfaces are identifiedand described in aconsistent way with clearownersThe data, personnel, devices, systems,and facilities that enable theorganisation to achieve businesspurposes are identified and managedconsistent with their relative importanceto business objectives and theorganisation’s risk strategy.No formal inventory ofsystems, theirinterdependencies andinterfacesAd hoc, not formalisedAll critical systems andinterfaces are identified anddescribed in a consistent waywith clear ownersPartialAd hoc, no formalisedassessment processThe organisation understands thecybersecurity risk to organisationaloperations (including mission, functions,image, or reputation), organisationalassets, and individuals, including system‐of‐system aspects resulting fromdependencies.No documented riskassessment processes orassessmentsAd hoc, no formalisedassessment processConsistent, organisation‐wideapplication with identified riskand requirement owners;Management‐approvedexternal validation of riskprocesses that lead to cyberlevels by authorities; Securityrequirements being identifiedrisk assessment is taken intoaccount in safety riskassessment, and vice versaNon‐existentNo, or very limited,cybersecurity informationsharingThe organisation obtains and sharesthreat intelligence, vulnerability andincident information activities, withinternal and external partiesThe organisation’s priorities, constraints,risk tolerances, and assumptions areSome requirements placed onestablished and used to support risksome suppliers andMinimum set of requirementsRequirements placed onIndependent reviews / audits /decisions associated with managingassessments supportingagreements with someplaced on all critical suppliers suppliers with proportionateNo complete overview of allregular updates ofpartners; partial and informaland agreements withcompliance checks andsupply chain risk. The organisation has insuppliers / partnersrequirements against ses/penalties/place the processes to identify, assessgood practicessupplier/partner cyber‐assessment for compliance measures for non‐complianceand manage supply chain risks.maturityAppropriate levels of trust areestablished with data exchange partners.Lead and GovernAsset ManagementRisk Assessment21Fully operatio
The high-level model is a really simple maturity assessment with 13 capabilities and a classic maturity model answer set, indicating what Level 3 means, and what Level 4 means, etc. This enables assessment in under an hour by someone who has a suitably broad overview of that organisation. Given the broad and holistic nature of the maturity