Transcription
EXECUTIVE BRIEFINGERP CYBER SECURITY 2021/Q1Troels Lindgaard, 1DigitalTrustFrederik Weidemann, Onapsis Inc.January 27th 202128 January 2021Executive Briefing: ERP Cyber Security 20211
AGENDA1.Perspectives on SAP cyber security2.Evolution of mission critical application cyber attacks3.Newest threats to SAP Systems4.How to prevent SAP security breaches28 January 2021Executive Briefing: ERP Cyber Security 20212
RISK OF DYING IN AN AIRPLANE?1:29 million(for EU & US airlines)Source statistic: Statisticsbrain.com, The Economist cheinlicher-1.2409131Photo by Nathan Hobbs on Unsplash28 January 2021Executive Briefing: ERP Cyber Security 20213
RISK OF DYING IN A CAR ACCIDENT1: 8303 (USA 2018)1:27255 (Germany 2019)Sources statistics:US s-mortality-riskGER https://www.adac.de/news/bilanz-verkehrstote/Photo by Clark Van Der Beken on Unsplash28 January 2021Executive Briefing: ERP Cyber Security 20214
RISK OF ERP DATA BREACHES1:2Source:IDC Survey – ERP Security: TheReality of Business Critical Application Protection28 January 2021Executive Briefing: ERP Cyber Security 20215
RISK OF BREACHESIt’s not a question if you’ll be breached,but when it will happen 28 January 2021Executive Briefing: ERP Cyber Security 20216
ERP BREACHES ARE NOT HAPPENING?}51%Source: IDC Survey – ERP Security: The Reality of Business Critical Application Protection28 January 2021Executive Briefing: ERP Cyber Security 20217
BUSINESS RISKS – DATA INTEGRITY – LOSS OF AUDIT TRAIL AND DATA RELIABILITYSource: IDC Survey – ERP Security: The Reality of Business Critical Application Protection28 January 2021Executive Briefing: ERP Cyber Security 20218
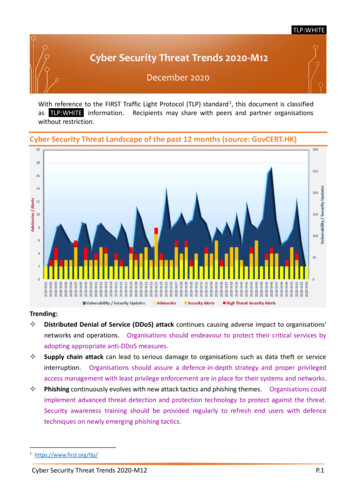
WORLD ECONOMIC FORUMTHE GLOBAL RISKS REPORT 2020Source: http://www3.weforum.org/docs/WEF Global Risk Report 2020.pdfWorld Economic Forum Global Risks Perception Survey 2019–202028 January 2021Executive Briefing: ERP Cyber Security 20219
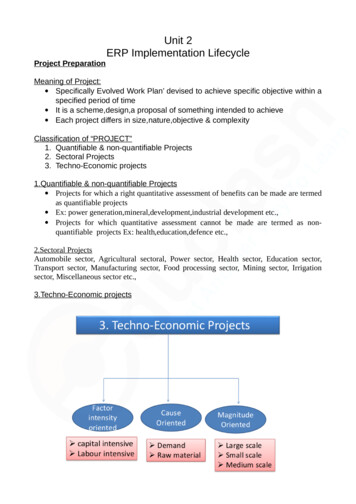
2020EVOLUTION OF MISSION-CRITICAL APPLICATION CYBERATTACKSEXPLOITTOOLKITSAP 1st public exploittargeting SAPapplicationsCYBERCRIMINALSCREATINGMALWARESAP targetedmalwarediscovered28 January 2021PUBLICEXPLOITChinesehackerexploits SAPNetWeaver2015NATION-STATESPONSOREDChinese breachof USIS targetedSAP1ST DHSUS-CERTALERTfor SAPBusinessApplicationsINCREASEDINTEREST ONDARK WEBOnapsis helpsOracle securecriticalvulnerabilityin EBSExecutive Briefing: ERP Cyber Security 20212ND DHSUS-CERTALERTfor SAPBusinessApplicationsDHS US-CERTALERT3RD DHS USCERT ALERTfor sBigDebITOracleVulnerabilities4th DHS USCERT ALERTfor SAP RECONVulnerabilityONAPSIS THREATINTEL
INTERNET EXPOSURE RECON JULY .09%Europe59823.82%Middle East1465.81%North eaniaSouth AmericaNot SpecifiedTotal28 January 2021Executive Briefing: ERP Cyber Security 202111
28 January 2021Executive Briefing: ERP Cyber Security 202112
SAP NETWEAVER IN FOCUS OF ZERODIUMZerodium isactivelysearching forSAP NetWeaverexploitsSource: https://zerodium.com, 26.10.202028 January 2021Executive Briefing: ERP Cyber Security 202113
CHALLENGE丨BLACK HAT USA 2020EXPLOITATION DEMONSTRATION OF SOLUTIONMANAGER1. Exploitation of EEM2. Exploitation of SMDagent3. Lateral movement with SAPControl escalating to rootprivileges on entire SAPlandscapeRemark:A public exploit for 1. (CVE-20206207 has been released on14.01.2021)28 January 2021Executive Briefing: ERP Cyber Security 202114
EXPLOITATION DEMONSTRATION OF SOLUTIONMANAGERExample Black Hat USA 2020: P. Artuso & Y. Genuer (Onapsis)28 January 2021Executive Briefing: ERP Cyber Security 202115
EXPLOITATION DEMONSTRATION OF SOLUTIONMANAGERExample Black Hat USA 2020: P. Artuso & Y. Genuer (Onapsis)28 January 2021Executive Briefing: ERP Cyber Security 202116
EXPLOITATION DEMONSTRATION OF SOLUTIONMANAGERExample Black Hat USA 2020: P. Artuso & Y. Genuer (Onapsis)RESULT:Root on SAP landscapeSAP ALL in all systems28 January 2021Executive Briefing: ERP Cyber Security 202117
BLACK HAT USA 2020: “AN UNAUTHENTICATED JOURNEY TO ROOTRelated SAP OSS Notes Patch 2902645 Patch 2902456 Patch 2890213 Patch 2808158 Patch 2823733 Patch 2839864 Patch 2849096 Patch 2772266 Patch 2738791 Patch 2748699 Patch 2845377 Patch 290493328 January e Briefing: ERP Cyber Security 202119
CHALLENGE丨SAP PATCH MANAGEMENT900Change of SAP’s securitystrategy in 2009e.g. static code analysisusage in ERP standardusing CodeProfiler800700Change of SAP’s patching strategySecurity notes are delivered with SPsdependingon their priority level600Change of SAP’spatching policy24 month rule500400Correction with low priorityCorrection with medium priorityCorrection with high priorityHotNews300There areHotNewsevery 820192020Source: https://support.sap.com/securitynotes – aggregated extract from Jan 202128 January 2021Executive Briefing: ERP Cyber Security 202120
BUSINESS CASE FOR ERP CYBER SECURITY PROTECTIONBUSINESS CASE – AVOID PROFIT LOSS Example: Cost for ERP Cyber security protection is 0,5-1% of the profit loss*BUSINESS CASE – AVOID SHARE PRICE DECLINE Example: Cost for ERP Cyber security protection is 0,01-0,02% of the loss in market value**BUSINESS CASE – AVOID EMERGENCY AND CLEAN UP COSTS Example: Cost for ERP Cyber security protection is 0,5 - 2 % of the Emergency and clean up costs**** Based on the reported profit loss from Maersk, Demant and ISS, compared with the average yearly cost for ERP Cyber security protection program.** Based on the share price loss from the attack is public and until the share price decline ends, from Maersk, Demant and ISS, compared with the average yearly cost for ERP Cyber security protection program.*** Based on the reported costs for emergency and clean up costs from Maersk, Demant and ISS, compared with the average yearly cost for ERP Cyber security protection program.28 January 2021Executive Briefing: ERP Cyber Security 202121
BUSINESS CASE – NO DOWNTIME Cost for an ERP Cyber security system is 1-5 hours of downtime for 2/3 of companiesSource: IDC Survey – ERP Security: The Reality of Business Critical Application Protection28 January 2021Executive Briefing: ERP Cyber Security 202122
BEST PRACTICES FOR 20211. Understand the technology you’re using2. Measure your security maturity level across your environment3. Setup a centralized security measurement control,e.g. build a SAP security dashboard4. Automate your security checks to avoid faulty settings28 January 2021Executive Briefing: ERP Cyber Security 202123
THE ONAPSIS PLATFORM MOST COMPREHENSIVE SOLUTION FORPROTECTING YOUR MISSION-CRITICAL APPLICATIONSMISSION-CRITICAL APPLICATIONSCUSTOMER RELATIONSHIP PRODUCT LIFECYCLE HUMAN CAPITAL SUPPLY CHAIN SUPPLIER RELATIONSHIP BUSINESS INTELLIGENCE28 January 2021ERP AssetsExecutive Briefing: ERP Cyber Security 2021SaaS Assets24
THE ONAPSIS PLATFORM – DASHBOARD28 January 2021Executive Briefing: ERP Cyber Security 202125
THE ONAPSIS PLATFORM – CODE SCANNING28 January 2021Executive Briefing: ERP Cyber Security 202126
THE ONAPSIS PLATFORM – EXAMPLE: SPLUNK INTEGRATION28 January 2021Executive Briefing: ERP Cyber Security 202127
SAP RISK, SECURITY AND COMPLIANCELicense Risk mitigation, review,optimization, clean upGDPR Deletion Subject access reporting AuthorizationsCompliance andFraud preventionBasic security SoD authorization concept Built in controls in SAP Control catalogue Control descriptions Control user guides Governance28 January 2021 Risk catalogue Logging / SIEM Cyber security System settings Coding Integrations Change Management(Transports) Standard authorization conceptExecutive Briefing: ERP Cyber Security 202128
1DIGITALTRUST APPROACH FOR RISK AND COMPLIANCE IN SAPAgree on Businesscase potentials andrisk scenarios?Business case and riskscenarios verified?Business case realizationand risk mitigationBusiness case realizationand risk mitigation123RISK ASSESSMENTIMPLEMENTATIONGOVERNANCE ANDCONTINUES MONITORING Basic security Compliance & fraudprevention GDPR Licenses28 January 2021 Basic security Compliance & fraudprevention GDPR LicensesExecutive Briefing: ERP Cyber Security 2021 Basic security Compliance & fraudprevention GDPR Licenses29
BUSINESS RISKILLUSTRATIONEnsuring application availability,streamlining audit processesand protecting the business fromrisk are essential.O P E R AT I O N A RRISKASSESSMENTPrevent applicationdowntime and costlybusiness disruptionEliminate resourceconsuming manual auditprocessesReduce vulnerabilitiesand misconfiguration toprotect the business
CALL TO ACTION NOW: ARE YOUR ERP SYSTEMS’ SECURE? Get a risk assessment of your SAP system – Business Risk Illustration (BRI) Executive Overview Do you have known risks? Next stepsRules of engagement Senior level commitment Technical verification of findings (Are controls already in place) Discuss outcome (risk to the business) and next steps1DigitalTrust is a SAP Cyber security, compliance and data privacy consultancy in the NordicsOnapsis is the leading ERP Cyber security vendor for SAP and Oracle.28 January 2021Executive Briefing: ERP Cyber Security 202131
CONTACT US & NEXT STEPSFrederik WeidemannTroels LindgårdE: frederik.weidemann@onapsis.comM: 49 151 18215 211E: troels.lindgaard@1digitaltrust.comM: 45 5363 ://www.onapsis.com/Contact for technical questions.28 January 2021Contact for demo, business case buildingor other questions.Executive Briefing: ERP Cyber Security 202132
APPENDIX
OUR BELIEFSOur overall belief is that Digital Trust is good for business;Trust creates loyalty, both for our clients and their customers.SUSTAINABILITYWe have a responsibility when doing business. As a new company we mustlive out the UN sustainable development goals (SDG) with a special focus onclimate. As an example we plant 1 tree for every billable hour #1Hour1Tree.We have therefore planted our first forest, 1DigitalTrust Forest, a forest withover 8.000 trees next to Gudenaaen in Jutland, Denmark.
1DIGITALTRUST SERVICESSAP Customer Data CloudSAP License ManagementData EthicsServicesSAP License ManagementservicesSAP S/4 License conversionsSAP Contract ReviewSAP License reviewsSAP License optimizationsSAP Indirect use analysis and optimizationsData EthicsSAP Cyber securityCodingIntegrationTransportSystem settingsSAP ComplianceAccess & Identity ManagementSAP Authorization ManagementSegregation of dutiesSecure LoggingGDPR Management ConsultingGDPR Project ManagementGDPR Compliance AssessmentGDPR in SAP – Data Analysis & DeletionILM accelerator for GDPR complianceSAP Customer Data CloudCIAM (Customer Identity & Access Management)SAP Customer Data Cloud ImplementationSAP Customer IdentitySAP Customer ConsentSAP Customer ProfileB2BIn a box solutionCDC in a boxConsent managementPartners
THE ONAPSIS PLATFORMASSESSCONTROLFind & RemediateSecurity Risks SAP and Oracle EBS systemmisconfigurations, patchesvulnerabilities, authorizationsDeployed SAP custom codefor security and quality errorsSAP system interfaces andcommunicationsIntegrations with workflow services:COMPLYManage Change;Avoid Disruption DEFENDAutomate Audit ProcessesIdentify security and qualityerrors in SAP custom code Lock and block SAPconfiguration changesIdentify and blocking SAPtransports with security issuesand errorsEvaluate compliance impact ofSAP System vulnerabilities,misconfigurations, patchesauthorizations, deployed code Out-of-the-box & custom policies Evaluate and verify IT controlsIntegrations with change managementand development environments:Continuous Threat Monitoring Near real-time attack alertsMonitor for SAP exploits ,threats, user activity /transactions, privilege misuseAlert for changes to SAP systeminterfaces, bad transportsIntegrations with SIEMs:SAP ChaRM, TMS, HANA Studio, Eclipse, WebIDE, ABAP development workbenchMANAGEMENT FUNCTIONALITYReporting &AnalysisTicketing/SOCIntegrationScheduling &WorkflowsAsset DiscoveryUsers & RoleManagement
SAP Customer Profile B2B In a box solution CDC in a box Consent management 1DIGITALTRUST SERVICES Data Ethics SAP Cyber security Coding Integration Transport System settings SAP Compliance Access & Identity Management SAP Authorization Management Segregation of duties Secure Logging GDPR Management Consulting GDPR Project Management GDPR .