Transcription
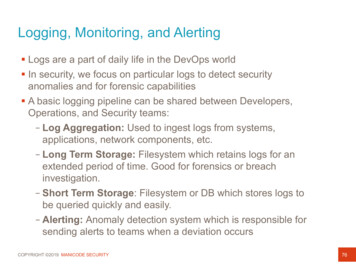
Logging, Monitoring, and Alerting§ Logs are a part of daily life in the DevOps world§ In security, we focus on particular logs to detect securityanomalies and for forensic capabilities§ A basic logging pipeline can be shared between Developers,Operations, and Security teams:– Log Aggregation: Used to ingest logs from systems,applications, network components, etc.– Long Term Storage: Filesystem which retains logs for anextended period of time. Good for forensics or breachinvestigation.– Short Term Storage: Filesystem or DB which stores logs tobe queried quickly and easily.– Alerting: Anomaly detection system which is responsible forsending alerts to teams when a deviation occursCOPYRIGHT 2019 MANICODE SECURITY76
Logging and Monitoring PipelineLong TermStorageIaaSLogAggregationShort TermStorageQuery InterfaceAnomalyCOPYRIGHT 2019 MANICODE SECURITYAlerting SystemDevSecOps77
Infrastructure as CodeCOPYRIGHT 2019 MANICODE SECURITY78
Building Infrastructure§Is your infrastructure §Self documenting?§Version controlled?§Capable of continuous delivery?§Integration tested?§Immutable?Remember: ”It’s all software"COPYRIGHT 2019 MANICODE SECURITY79
Immutable Infrastructure“Immutable infrastructure is compromised of components which arereplaced during deployment rather than being updated in place”COPYRIGHT 2019 MANICODE SECURITY80
Security and Immutable Infrastructure§An immutable infrastructure starts with a“Golden Image” in a version catalog§Security teams have a central location tovalidate images as compliant and enforce OShardening policies§No more guesswork what is installedAutomation can flag security anomalies vs.human intervention§Tags help teams wrangle infrastructure“Push Security to the Left”COPYRIGHT 2019 MANICODE SECURITY81
Simple Immutable InfrastructureInstance 1Version CatalogBaseImageBaseImage0.20.2Base OSPackagesInstance 2BaseImage0.2Base ContainerLatest CodeInstance nBaseImage0.2COPYRIGHT 2019 MANICODE SECURITY82
Proving Immutability96c5 07e4bbInstance 1SHA1(Base Image)Version CatalogBaseImageBaseImage0.20.2Base OSPackages96c5 07e4bbInstance 2BaseImage0.2Base Container96c5 07e4bbInstance nLatest CodeBaseImage0.2COPYRIGHT 2019 MANICODE SECURITY83
Shellshock?Instance 1Version CatalogBaseImageBaseImage0.20.2Base OSPackagesInstance 2BaseImage0.2Base ContainerLatest CodeInstance nBaseImage0.2COPYRIGHT 2019 MANICODE SECURITY84
Shellshock?Instance 1Version CatalogBaseImageBaseImage0.30.3Base OSInstance 2PackagesBaseImage0.3Base ContainerInstance nLatest CodeEmergencyPatch!COPYRIGHT 2019 MANICODE SECURITYBaseImage0.385
Cattle, not pets.COPYRIGHT 2019 MANICODE SECURITY86
Security Wins§Security team now has insight into the entiresystem§Infrastructure is auditable and versioncontrolled, just like source code§Patching can be applied programmatically witha high level of certainty§Alerting can be built for changes to specificareas of the infrastructure– A new firewall rule is created or deleted– Administrative user is created– New VPC rolled out§Testing can occur much earlier in the pipelineCOPYRIGHT 2019 MANICODE SECURITY87
Infrastructure as Code - TerraformCOPYRIGHT 2019 MANICODE SECURITY88
Infrastructure as Code – K8sCOPYRIGHT 2019 MANICODE SECURITY89
”Chaos” TestingCOPYRIGHT 2019 MANICODE SECURITY90
Brief Introduction to ContainersCOPYRIGHT 2019 MANICODE SECURITY91
Containers, Containers, Containers, Containers COPYRIGHT 2019 MANICODE SECURITY92
Software Deployment is Changing§Massive shift toward cloud computing§Increased demand for application and infrastructureportability across environments§Avoid vendor “lock in” when possibleProcess§Increase in microservicesAKASecurityloosely coupled servicesProcess IsolationCOPYRIGHT 2019 MANICODE SECURITY93
Modern Applications§Breaking monolithic applications into smaller servicesoffers several advantages:- Scale independently- Stateless- High Availability- API-Driven- Faster iteration timesCOPYRIGHT 2019 MANICODE SECURITYProcess SecurityProcess Isolation94
Issues with Modern Applications§Organizations often operate in an Ops vs. Dev vs. Secworld§Applications and microservices are written in a variety oflanguages and frameworksProcessSecurity§Applications need to runon differenttechnology stacks:–Virtual MachinesProcess Isolation–Windows Server–Bare Metal Servers–Cloud Environments–On-Prem Environments–Developer LaptopsCOPYRIGHT 2019 MANICODE SECURITY95
ApplicationOperating SystemPhysical ServerCOPYRIGHT 2019 MANICODE SECURITYPhysicalHost
ApplicationOperating SystemPhysical ServerCOPYRIGHT 2019 MANICODE SECURITY§One application per server§Slow deployment times§Low resource utilization§Scaling challenges§Migration challenges§ §Difficult to replicate locally
Physical orHost Operating SystemCOPYRIGHT 2019 MANICODE SECURITYVM
Physical orHost Operating SystemCOPYRIGHT 2019 MANICODE SECURITY§One physical server andmultiple applications§Each application runs in aVirtual Machine§Better resource utilization§Easier to scale§VMs live in the Cloud§Still requires completeguest Operating Systems§Application portability notguaranteed
Physical ServerContainerContainerContainerApp 1App 2App 3BinsLibsBinsLibsBinsLibsDocker (CRI)Host Operating SystemCOPYRIGHT 2019 MANICODE SECURITYContainer
Physical ServerContainerContainerContainerApp 1App 2App 3BinsLibsBinsLibsBinsLibsDocker (Container Runtime)Host Operating SystemCOPYRIGHT 2019 MANICODE SECURITY§Containers are anapplication layer construct§VMs allow us to convertone physical machine intomany servers§No Operating System toboot (fast!)§Most portable out of alloptions§Less OS overhead usingshared kernel model
Physical ServerVM 1VM 2VM 3ContainerContainerContainerApp 1App 2App rvisorHost Operating SystemCOPYRIGHT 2019 MANICODE SECURITYContainersand VMsare HappyTogether
It's been a pleasure.jmesta@manicode.comJimmy Mesta Secure Coding Instructor www.manicode.com
Logging, Monitoring, and Alerting 76 §Logs are a part of daily life in the DevOps world . -A new firewall rule is created or deleted -Administrative user is created -New VPC rolled out §Testing can occur much earlier in the pipeline. . Virtual Machine


![REST API Penetration Testing Report for [CLIENT] - UnderDefense](/img/36/anonymised-api-penetration-testing-report.jpg)