Transcription
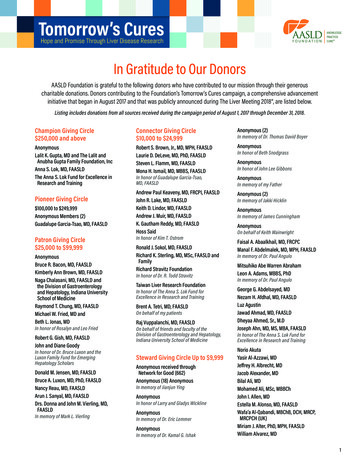
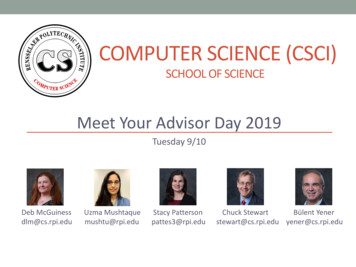
Anonymous CommunicationMatt EdmanImages and some slides by Roger Dingledineedmanm2@cs.rpi.eduCSCI-4220 Network ProgrammingRensselaer Polytechnic InstituteAnonymous Communication – p. 1/3
OverviewWhat is anonymity and why should I care?High-Latency SystemsMessage-basedLow-Latency SystemsConnection-orientedFuture work and unsolved problemsAnonymous Communication – p. 2/3
Introduction‘ ‘Anonymity is the state of being notidentifiable within a set of subjects, theanonymity set.” – Pfitzmann and KöhntoppAnonymous Communication – p. 3/3
Anonymous From Whom?Sender/Recipient Anonymity Channel and Data AnonymityOutside observer / Network insider Channel AnonymityCommunicant identification should notbe a property of the channel.Anonymous Communication – p. 4/3
Anonymous From Whom?AdversariesInternal or ExternalPassive or ActiveLocal or GlobalStatic or AdaptiveAnonymous Communication – p. 5/3
Who Needs Anonymity?Myth:“Criminals are the onlypeople who want anonymity.”Anonymous Communication – p. 6/3
Who Needs Anonymity?Myth:“I encrypt my Internettraffic, so I’m okay.”Anonymous Communication – p. 7/3
Who Needs Anonymity?YouWhat are you Googling for?What websites do you visit?CorporationsProtection for employees“Competitive Analysis”Anonymous Communication – p. 8/3
Who Needs Anonymity?Intelligence AgenciesIntelligence gatheringInternational CoalitionsLaw EnforcementAnonymous Tip LinesHoneypots and stingsVoters/ElectionsAnonymous Communication – p. 9/3
Anonymity Loves CompanyYou can’t be anonymous by yourselfYou don’t want trust your anonymity toone entity, eitherDistributed trustDiversity and dispersal of securityrequirementsAnonymous Communication – p. 10/3
Technical ApproachesMixesHigh-latency (email)ProxiesLow-latency (www, ssh, irc, etc.)Anonymous Communication – p. 11/3
High-Latency AnonymityAnonymous Communication – p. 12/3
MixesDecrypts and randomly permutes dataAnonymous Communication – p. 13/3
MixesWhich input was message 2?Anonymous Communication – p. 14/3
MixesChaumian Mix NetworkAnonymous Communication – p. 15/3
MixesCiphertext EP K1 [EP K2 [EP K3 [message]]]Anonymous Communication – p. 16/3
MixesAnonymous Communication – p. 17/3
MixesOnly need 1 non-compromised mix to be secureAnonymous Communication – p. 18/3
Mixing StrategiesThreshold Mixn 1 attackTimed MixTrickle attackPool MixesThreshold pool mixTimed pool mixTimed dynamic-pool mix (Cottrell Mix)Anonymous Communication – p. 19/3
Deployed Remailersanon.penet.fiMapped pseudonym to identityLegal attacks by the Church of Scientology (1995)Cypherpunks remailer (Type I)No delayingMixmaster (Type II)Added pools and messsage paddingMixminion (Type III)Added reply blocks/anonymous recipientsUsed TLS for link encryptionAnonymous Communication – p. 20/3
I’m ImpatientLow-Latency AnonymityAnonymous Communication – p. 21/3
ProxiesCentralized TrustExample: anonymizer.comAnonymous Communication – p. 22/3
Tor“The Second-Generation Onion Router”Roger Dingledine and Nick MathewsonBased on work from the NRLUse public-key crypto for establishingcircuitsUse symmetric-key crypto to move dataAnonymous Communication – p. 23/3
Building a CircuitClient negotiates key with first hopEphemeral Diffie-Hellman w/ RSAAnonymous Communication – p. 24/3
Building a CircuitClient tunnels through first hopNegotiates key with second hopAnonymous Communication – p. 25/3
Building a CircuitClient tunnels through first and second hopsNegotiates key with third hop (exit node)Anonymous Communication – p. 26/3
Building a CircuitCircuit establishedExit node connects to destinationAnonymous Communication – p. 27/3
Building a CircuitStreams can reuse the same circuitSaves on expensive public key cryptoKeys tossed when circuit is torn downAnonymous Communication – p. 28/3
Directory ServersLets clients learn about serversDirectories signed by authoritativedirectory serversMirrored by other serversControlled by humansTries to prevent Sybil attacksTrust bottleneckAnonymous Communication – p. 29/3
Threat ModelAssumes end-to-end attacks are trivialAssumes an adversary owns some ofthe nodesNo mixing or paddingWeaker than most in previous literature.but it’s actually usableAnonymous Communication – p. 30/3
AttacksDNS Leakage (not Tor’s fault)Timing-attacksWebsite fingerprintingPartitioning AttacksTor isn’t really vulnerable to thisunless the client is not smart?Anonymous Communication – p. 31/3
Legal IssuesExit nodes get hassled fairly frequentlyDMCA noticesEFF wants a person willing to get sued(seriously)Eavesdropping by exit nodes“If you want to be treated like acarrier, act like one”Anonymous Communication – p. 32/3
Related WorkFreedom NetworkZero-Knowledge SystemsUDP-basedCommercially-fundedR.I.P.Anonymous Communication – p. 33/3
Related WorkCrowdsWeb-based anonymityPlausible deniabilityForwards traffic within members of ajondoNo encryptionAnonymous Communication – p. 34/3
Related WorkJAPJava Anon ProxyUniversity of DresdenUses cascades instead of free-routesBackdoored in 2003 due to a courtorderSuccessfully fought in courtAnonymous Communication – p. 35/3
Related WorkTarzan and MorphmixFully p2pPerhaps more scalable (maybe)You lose if you pick a bad entry nodeMorphmix adds collusion resistanceAnonymous Communication – p. 36/3
Semi-Related WorkBlossomGeoff Goodell - HarvardApproach to overcoming InternetfragmentationUses Tor as a substrateAnonymous Communication – p. 37/3
Future WorkIncentivesGetting people to run a server?Paying people sure didn’t workPaddingDoes it help?Global adversariesDo they exist?Anonymous Communication – p. 38/3
QuestionsQuestions/Discussions?Anonymous Communication – p. 39/3
edmanm2@cs.rpi.edu CSCI-4220 Network Programming Rensselaer Polytechnic Institute Anonymous Communication - p. 1/39. Overview . Anonymous Communication - p. 20/39. I'm Impatient Low-Latency Anonymity Anonymous Communication - p. 21/39. Proxies Centralized Trust Example: anonymizer.com