Transcription
Packet Sniffing and SpoofingCS 335: Special Topic in Cyber Security
How Packets Are Received NIC (Network Interface Card) is a physical or logical linkbetween a machine and a network Each NIC has a MAC address Every NIC on the network will hear all the frames on the wire NIC checks the destination address for every packet, if theaddress matches the cards MAC address, it is further copiedinto a buffer in the kernelCS 335: Special Topic in Cyber Security2
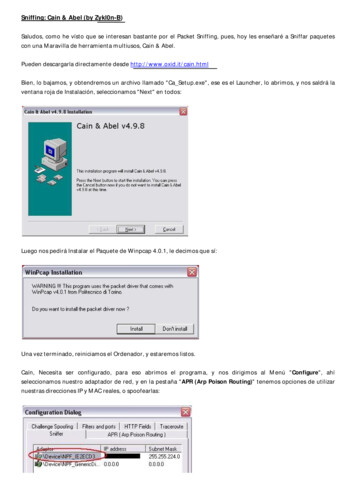
Promiscuous Mode The frames that are not destined to a given NIC are discarded When operating in promiscuous mode, NIC passes every framereceived from the network to the kernel If a sniffer program is registered with the kernel, it will be ableto see all the packets In Wi-Fi, it is called Monitor ModeCS 335: Special Topic in Cyber Security3
2.4 ChannelsCHANNELS 1, 6, 11DON’T OVERLAP WITHONE ANOTHERCS 335: Special Topic in Cyber Security4
BSD Packet Filter (BPF) BPF allows a userprogram to attach afilter to the socket,which tells the kernelto discard unwantedpackets. An example of thecompiled BPF code isshown here.CS 335: Special Topic in Cyber Security5
BSD Packet Filter (BPF)setsockopt(sock, SOL SOCKET, SO ATTACH FILTER, &bpf, sizeof(bpf)) A compiled BPF pseudo-code can be attached to a socketthrough setsockopt() When a packet is received by kernel, BPF will be invoked An accepted packet is pushed up the protocol stack. See thediagram on the following slide.CS 335: Special Topic in Cyber Security6
Packet Flow With/Without FiltersCS 335: Special Topic in Cyber Security7
Packet SniffingPacket sniffing describes the process of capturing live dataas they flow across a networkLet’s first see how computers receive packets.CS 335: Special Topic in Cyber Security8
IPv4 address structure Port numbers and IP addresses are in *network byte order*.CS 335: Special Topic in Cyber Security9
Addresses INADDR LOOPBACK (127.0.0.1) always refers to the local host via the loopback device INADDR ANY (0.0.0.0) means any address for binding INADDR BROADCAST (255.255.255.255) means any hostCS 335: Special Topic in Cyber Security10
Functions Create an endpoint for communication- int socket(int domain, int type, int protocol); Bind a name to a socket- int bind(int sockfd, const struct sockaddr *addr, socklen t addrlen); Receive message from socket- ssize t recvfrom(int sockfd, void *buf, size t len, int flags, struct sockaddr *src addr,socklen t *addrlen);CS 335: Special Topic in Cyber Security11
Receiving Packets Using SocketCreate thesocketProvideinformation aboutserverReceivepacketsCS 335: Special Topic in Cyber Security12
Receiving Packets Using Raw SocketCreating a raw socketCapture all types of packetsEnable thepromiscuousmodeWait for packetsCS 335: Special Topic in Cyber Security13
Limitation of the Approach This program is not portable across different operating systems. Setting filters is not easy. The program does not explore any optimization to improve performance. The PCAP library was thus created.-It still uses raw sockets internally, but its API is standard across all platforms. OS specificsare hidden by PCAP’s implementation.-Allows programmers to specify filtering rules using human readable Boolean expressions.CS 335: Special Topic in Cyber Security14
Packet Sniffing Using the pcap APIInitialize a rawsocket, set thenetwork deviceinto promiscuousmode.FilterInvoke this function for every captured packetCS 335: Special Topic in Cyber Security15
Processing Captured Packet: Ethernet HeaderThe packet argumentcontains a copy of thepacket, including theEthernet header. Wetypecast it to the Ethernetheader structure.Now we can accessthe field of thestructureCS 335: Special Topic in Cyber Security16
Ethernet FrameCS 335: Special Topic in Cyber Security17
Processing Captured Packet: IP HeaderFind where the IPheader starts, andtypecast it to the IPHeader structure.Now we can easilyaccess the fields in theIP header.CS 335: Special Topic in Cyber Security18
Further Processing Captured Packet If we want to further process the packet, such as printing out theheader of the TCP, UDP and ICMP, we can use the similar technique.- We move the pointer to the beginning of the next header and type-cast- We need to use the header length field in the IP header to calculate the actual sizeof the IP header In the following example, if we know the next header is ICMP, wecan get a pointer to the ICMP part by doing the following:CS 335: Special Topic in Cyber Security19
Packet Spoofing When some critical information in the packet is forged, we refer to it as packetspoofing. Many network attacks rely on packet spoofing. Let’s see how to send packets without spoofing.CS 335: Special Topic in Cyber Security20
Sending Packets Without SpoofingTesting: Use the netcat (nc)command to run a UDP serveron 10.0.2.5. We then run theprogram on the left from anothermachine. We can see that themessage has been delivered tothe server machine:CS 335: Special Topic in Cyber Security21
Spoofing Packets Using Raw SocketsThere are two major steps in packet spoofing:- Constructing the packet- Sending the packet outCS 335: Special Topic in Cyber Security22
Spoofing Packets Using Raw SocketsWe use setsockopt() toenable IP HDRINCL on thesocket.For raw socketprogramming, since thedestination information isalready included in theprovided IP header, we donot need to fill all the fieldsSince the socket type is rawsocket, the system will sendout the IP packet as is.CS 335: Special Topic in Cyber Security23
Spoofing Packets: Constructing the PacketFill in the ICMP HeaderFind the starting pointof the ICMP header,and typecast it to theICMP structureFill in the ICMPheader fieldsCS 335: Special Topic in Cyber Security24
Spoofing Packets: Constructing the PacketFill in the IP HeaderTypecast the buffer tothe IP structureFill in the IP headerfieldsFinally, send out the packet:CS 335: Special Topic in Cyber Security25
Spoofing UDP PacketsConstructing UDPpackets is similar, exceptthat we need to includethe payload data now.CS 335: Special Topic in Cyber Security26
Spoofing UDP Packets (continued)Testing: Use the nc command to run a UDP server on 10.0.2.5. Wethen spoof a UDP packet from another machine. We can see that thespoofed UDP packet was received by the server machine.CS 335: Special Topic in Cyber Security27
Sniffing and Then Spoofing In many situations, we need to capture packets first, and then spoof a response based onthe captured packets. Procedure (using UDP as example)- Use PCAP API to capture the packets of interests- Make a copy from the captured packet- Replace the UDP data field with a new message and swap the source and destination fields- Send out the spoofed replyCS 335: Special Topic in Cyber Security28
UDP PacketCS 335: Special Topic in Cyber Security29
UDP Packet (Continued)CS 335: Special Topic in Cyber Security30
Packing Sniffing Using ScapyCS 335: Special Topic in Cyber Security31
Spoofing ICMP & UDP Using ScapyCS 335: Special Topic in Cyber Security32
Sniffing and Then Spoofing Using ScapyCS 335: Special Topic in Cyber Security33
Packet Spoofing: Scapy v.s C Python Scapy- Pros: constructing packets is very simple- Cons: much slower than C code C Program (using raw socket)- Pros: much faster- Cons: constructing packets is complicated Hybrid Approach- Using Scapy to construct packets- Using C to slightly modify packets and then send packetsCS 335: Special Topic in Cyber Security34
Endianness Endianness: a term that refers to the order inwhich a given multi-byte data item is stored inmemory.- Little Endian: store the most significant byte ofdata at the highest address- Big Endian: store the most significant byte ofdata at the lowest addressCS 335: Special Topic in Cyber Security35
Endianness In Network Communication Computers with different byte orders will “misunderstand” each other.- Solution: agree upon a common order for communication- This is called “network order”, which is the same as big endian order All computers need to convert data between “host order” and “network order” .CS 335: Special Topic in Cyber Security36
Summary Packet sniffing- Using raw socket- Using PCAP APIs Packet spoofing using raw socket Sniffing and the spoofing EndiannessCS 335: Special Topic in Cyber Security37
CS 335: Special Topic in Cyber Security How Packets Are Received NIC (Network Interface Card) is a physical or logical link between a machine and a network Each NIC has a MAC address Every NIC on the network will hear all the frames on the wire NIC checks the destination address for every packet, if the address matches the cards MAC address, it is further copied