Transcription
Surveillance Detection
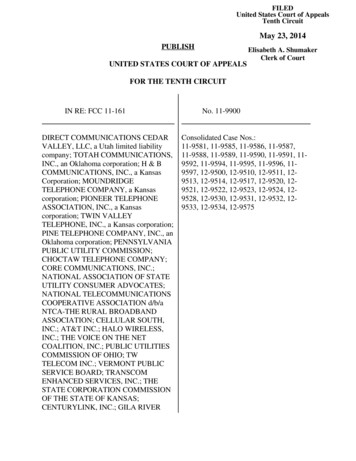
Terminal Performance Objective Provide you with an awareness of themost common types of surveillance andthe proactive measures you can take tohelp from becoming a target
Enabling PerformanceObjectives Identify the methods of conducting surveillanceExplain the attack cycleDiscuss the difference between a hard targetand a soft targetExplain choke points
Enabling PerformanceObjectives Identify descriptors of people and vehiclesDiscuss surveillance detection techniquesDescribe what to do if you suspectsurveillanceDiscuss how to avoid being a targetExplain attack recognition and response
Purpose of SurveillanceIntelligence Services – Information Criminal – Financial Terrorist – Terror (Further Political /Religious / Other goals)
The Attack Cycle
Target Selection
Hard Target vs. Soft TargetTime and PlaceUN-PREDICTABLEPREDICTABLE
Time Add stops or errands toincrease unpredictabilityExplore variable workscheduleVary by 30-60 minutes ormore!
Place Many attacks occur while targets in transit Choke Points – Areas you must pass through,residence and work are common ones Ideal Attack Sites:– Place where victim can be controlled with limitedavenues of escape– Location is well suited for surveillance and abilityto blend in to the environment
Route AnalysisLocate frequented venues Map five different routes to and fromeach venue Identify chokepoints Identify ideal attack sites Find safehavens Vary Randomly!
Detecting the SurveillanceBe alert – study details, especially atchoke points Know what is normal / not normal Gather descriptive information for yoursecurity office
Descriptors - PeopleGender Race Height – 2 inch increments Age – 5 year increments Weight – 10 pound increments Hair color/style, clothing, jewelry Distinguishing features
Descriptors - Vehicles ColorBody style and size– Number of doors Make, model and yearLicense number and originPeculiarities– Damage / decals / bumperstickers / custom features
Behavioral CuesTarget Fixation
Behavioral CuesPhotographyNote-taking
Behavioral CuesTime-Checking
Persons or Vehicles Persons / vehicles with nopurpose for being thereBroken down vehicles / taxis /vendors / service personnelIllegally parked vehicles or facingwrong way on one-way streets
Correlations Repeated sightings – same person orvehicle at different locations Rule of Three Report anything suspicious – it maycorrelate with something reported byanother person
If You Suspect SurveillanceConceal your suspicions - do notconfront Discreetly observe the person or vehicleto obtain a description Try to confirm surveillance Notify your security office
Avoid Being a TargetMaintain a low profile Vary your times and routes Be aware and alert - especially in chokepoints Allow yourself room to maneuver Be prepared to react - have a plan Know locations of safehavens
Attack Recognition SignsFocus on the choke points Target identification signals Strange / unusual behavior Something or someone slowing orstopping you, blocking vehicle Individuals approaching you rapidly Transition to weapons
Response to an Attack If you spot a potential attack ahead – do notgo there!Disrupt the attack!Create space between you and the threatMove quickly, do somethingBreak traffic laws if necessaryGet off of the XContact your security office
SummaryBe a hard target - Vary your times androutes Conduct Route Analysis – chokepointsand safehavens Surveillance is that unusual or abnormalbehavior Report surveillance right away Respond to an attack – take action
Surveillance Detection . Terminal Performance Objective Provide you with an awareness of the most common types of surveillance and the proactive measures you can take to help from becoming a target . Enabling Performance Objectives Identify the methods of conducting surveillance Explain the attack cycle Discuss the difference between a hard target and a soft target Explain choke points .