Transcription
MARKET RESEARCH,SECURITY CHALLENGES &ESET SOLUTIONSMichal Jankech, Principal Product Manager, ESET HQ
Michal JankechPrincipal Product Manager
User Research
User ResearchCo-DesignMarket Research Usability Testing BETAUserPartnerFeedback FeedbackAnalytics Telemetry
Enterprise Research2017-2019
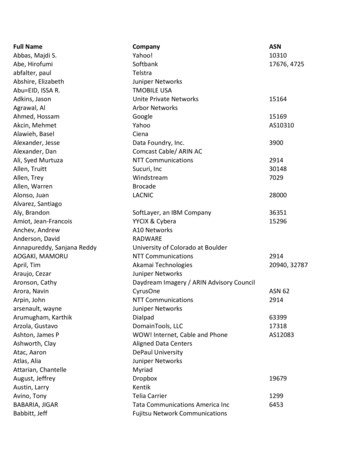
ties4%Telco2%Services2%
5 000 - 10 00015%2 000 - 5 00028%1 000 - 2 00018%10 000 - 20 00022%20 000 4% 1 00013%
AdministratorsOther EmployeesCompaniesUser PersonasServed PersonasOrganizational Personas
AdministratorsSophisticated AdministratorBasic Administrator
Sophisticated Administrator Lead by CISO Motivated, capable, eager to improve Formal teams and roles Wants to automate & integrate Likes and utilizes ESET capabilities
Basic Administrator Small, informally organized teams Often leads IT-Security Limited time, motivation and abilities Wants help and fire & forget behavior Struggles with complexity
Other EmployeesCISOTypical EmployeeEmpowered Employee
Chief Information Security Officer Key factor on many decisions Often established IT Security Sets the direction for adv. teams Passive user of ESMC Interested in reports & auditing
Typical Employee Limited rights on the computer Minimal knowledge about IT Security Majority of employees Security should be invisible
Empowered Employee Permissive company culture Technical users such as developers Semi-managed systems Has and sometimes uses admin access Benefits from some control
CompaniesTop-down CorporationDecentralized Organization
Top-down Corporation Typical hierarchical structure Clear responsibilities Centralized decision-making Administrators have control
Decentralized Organization Different regions with autonomy Consensus-focused culture Sometimes hierarchical structure Top-level decisions serve as guidance Applies to both use and purchase
Top challenges
What our customers percieve as „the challenge“ ?RansomwareTargeted attacks & hackingDiversified landscapeLack of network visibility &pressure on operational effectivenessEmployee misbehaviorLack of workforce
Cloud Sandbox(Dynamic ThreatDefense)Stops ransomwareupon entrySignature-lessdetection(RansomwareShield)EDR (EnterpriseInspector)Post attackdetection ofransomwareBehavior-basedprevention focusing behaviorRansomwareon changes insystem and content(what was changed, when,and how – and by what /whom)
Targeted Attacks & HackingMulti-layeredprevention(UEFI Scanner, ExploitBlocker, AMS)CentralizedReduce theattack surface management2FA for all admins(EEI & EDTDMap the holes and & ESMC)install patchesFinding the needle in ahaystack approach
Diversified LandscapeAt least one mac isalways in there(management /designer)Linux is gainingmomentumin government & ICS(SCADA)Centralizedmanagement withsoftware / hardwareasset managementESMC – providing software /hardware inventory for allplatforms with advancedfiltering
Lack of network visibility&Reportingpressure onHardware/softwareoperational effectivenessData consolidation& Notificationsinventory solutions focusingon reducing IT(sec)workloads(All data in onesystem – ESMC details in purposebuilt systems(EDTD / EEI))
Web control, time-based blockingDevice control, time-based blockingEmployeemisbehaviorReports (about potentiallyharmful activity)EDR with customization & UEBA (Enterpriseinspector rules, focusing on employee behavior(what they really do))
ConsultLackCoooperateof workforceOutsourceDeploymentServicesHelp to deployand setupproperlyThreat HuntingHelp to identifymalicious activitywhen neededThreatIntelligenceHelp to providesecurity context
How ESET helps?
By products .ESET ThreatIntelligenceESET EnterpriseInspectorESET Endpoint 7& Server ProductsESET DynamicThreat DefenseESET SecurityManagement Center
. That Fits Gartner CARTA frameworkESETThreatPREDICTIntelligenceESET EnterpriseRESPONDInspectorESETEndpoint7PREVENT& Server ProductsESETDynamicDETECTThreat CenterASSESMENT
Key takeaways?Next week: Upgrade your security product to the latest version Collect inventory across ALL your environment (software, hardware,appliances)Next three months: Consider enabling 2FA for all users with admin rights (stolen passwordis still responsible for 80% of all breaches) Develop a “Threat Feed” to cross-reference CVEs against yourinventory build a dashboard using the three data feeds
Useful linksVulnerability data feeds: MitreCVE Data Feed: https://cve.mitre.org/cve/data feeds.html NIST National Vulnerability Database (NVD):https://nvd.nist.gov/vuln/data-feeds Microsoft KB info: on.aspx?id 36982Check if your e-mail and password was not involved in a data breach https://haveibeenpwned.com/
Thank you!Questions?
/ESET@ESET#ESETDay esetglobal
MARKET RESEARCH, SECURITY CHALLENGES & ESET SOLUTIONS Michal Jankech, Principal Product Manager, ESET HQ