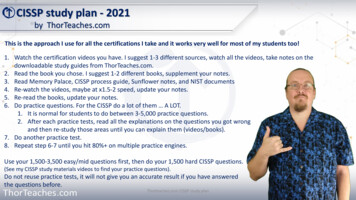
Transcription
Compliance Through SecurityJeff Wilder CISSP,ISSAP,ISSMP,CISA,CGEITPCI Security Standards CouncilControlCase Annual Conference – Orlando, Florida USA 2015
Question?If you found out that you were going to bebreached tomorrow, would you do anythingdifferent?If there are, why are you not doing them today?ControlCase Annual Conference – Orlando, Florida USA 20152
Information Security is ComplicatedControlCase Annual Conference – Orlando, Florida USA 20153
Verizon Breach Report Statistics2014 & 2015 DataControlCase Annual Conference – Orlando Florida USA 2015
No one is immune from attack or breach(Verizon 2015 Data Breach Investigation Report 3)ControlCase Annual Conference – Orlando, Florida USA 20155
Threat vectorsWho is getting to your data?3% Partner12% Internal85% External(Verizon 2015 Data Breach Investigation Report 4)ControlCase Annual Conference – Orlando, Florida USA 20156
Attack VectorsHow are they getting the data? Compromised CredentialsRam ScrapersKey LoggersPhishing Attack(Verizon 2015 Data Breach Investigation Report 5)ControlCase Annual Conference – Orlando, Florida USA 20157
Is it really that easy?- “About half of the CVEs exploited in 2014 went from publish topwn in less than a month.”- “We found that 99.9% of the exploited vulnerabilities had beencompromised more than a year after the associated CVE waspublished.”(Verizon 2015 Data Breach Investigation Report 11)ControlCase Annual Conference – Orlando, Florida USA 20158
Once they are in?Chilling Statistics: 87% of the POS systems werecompromised in less than an hour 89% of the compromised POSsystems had data exfiltrated in lessthan an hour after compromise 86% of the compromised POS systemswere discovered in less than a month(Verizon 2014 Data Breach Investigation Report 16)ControlCase Annual Conference – Orlando, Florida USA 20159
How is the breach discovered?“ 99% of the notifications wereexternal parties (primarilyCSIRTs) contacting victims to letthem know their hosts wereinvolved in other attacks”(Verizon 2014 Data Breach Investigation Report 21)ControlCase Annual Conference – Orlando, Florida USA 201510
Big data breaches 2014 Neiman MarcusWhite LodgingSally BeautyMichaels11 casinosNew YorkPF ChangsAlbertsons & SuperValuCommunity Health SystemsUPS Dairy QueenGoodwillHome DepotJimmy John’sJP Morgan ChaseSourcebooksKmartStaplesBebeSonyThe Big Data Breaches of 2014, ForbsControlCase Annual Conference – Orlando, Florida USA 201511
Compliance vs. SecurityControlCase Annual Conference – Orlando Florida USA 2015
Compliance vs. SecurityCompliance does not make you secureCompliance - The act or process of doing what you have beenasked or ordered to doSecurity -The state of being protected or safe from harm“Compliance is asking you to put a lock on the door. Security is making sureyou lock it every day.”(Bob Russo)Merriam-WebsterControlCase Annual Conference – Orlando, Florida USA 201513
Becoming SecureSo how do we get from compliance to security Many of the security frameworks do not include controls around: Governance and Oversight Metrics and Reporting Security frameworks are generally a one-size-fits-most and donot account for your: Individual business drivers Organizational size ComplexityControlCase Annual Conference – Orlando, Florida USA 201514
Are you a good gardener?ControlCase Annual Conference – Orlando, Florida USA 201515
Becoming SecureGovernance and Oversight Are your controls truly effective? How do you ensure their ongoing continuity? Do you have executive oversight?ControlCase Annual Conference – Orlando, Florida USA 201516
Going above and beyondAre your controls truly effective and address the RISK? Anti-malware Authentication Vulnerability identificationControlCase Annual Conference – Orlando, Florida USA 201517
Going above and beyond ComplianceHow do you ensure their ongoing continuity? Can you affirm with 100% certainty that you are secure this verymoment?ControlCase Annual Conference – Orlando, Florida USA 201518
Going above and beyond ComplianceDo you have executive oversight? What is your company’s strategic plan for security? To whom does your security team report to? Do you have the right people and business partners to help? What about vendor management? How are the resources for security allocated? Is your spend today a good value and provide benefit tomorrow?ControlCase Annual Conference – Orlando, Florida USA 201519
Closing Thoughts and ConsiderationsIf you don’t need it, get rid of itDevalue the dataInvest in good peopleImplement a robust training programBe proactiveFind a good business partner to help and provide youguidance7. Acquire the right tools8. Information share with organizations within your same vertical9. There are limitations in doing what needs to be done vs whatshould be done.1.2.3.4.5.6.ControlCase Annual Conference – Orlando, Florida USA 201520
Things To Take Away Being complaint does not ensure that you are secure Focus on truly being secure, compliance will follow Security is not an event, Is not an end state- it’s a processControlCase Annual Conference – Orlando, Florida USA 201521
Questions?ControlCase Annual Conference – Orlando Florida USA 201522
Work CitedMerriam-Webster. Merriam-Webster, n.d. Web. 13 Oct. 2015."The Big Data Breaches of 2014." Forbes. Forbes Magazine, 13 Jan. 2015. Web. 13Oct. 2015.Verizon 2015 Data Breach Investigation Report. Rep. 2015 ed. Virginia: Verizon, 2015.PrintControlCase Annual Conference – Orlando, Florida USA 20151
Jeff Wilder CISSP,ISSAP,ISSMP,CISA,CGEIT PCI Security Standards Council. ControlCase Annual Conference -Orlando, Florida USA 2015 If you found out that you were going to be breached tomorrow, would you do anything different? If there are, why are you not doing them today? 2