Transcription
CAS-002CASPA Success Guide to PrepareCompTIA Advanced Security Practitioneredusum.com
CASP- Success GuideTable of ContentsIntroduction to CAS-002 Exam on CompTIA Advanced Security Practitioner . 2CompTIA CAS-002 Certification Details: . 2CompTIA CAS-002 Exam Syllabus: . 3CAS-002 Sample Questions: . 17Answers to CAS-002 Exam Questions: . 19CAS-002 - CompTIA Advanced Security Practitionerpg. 1
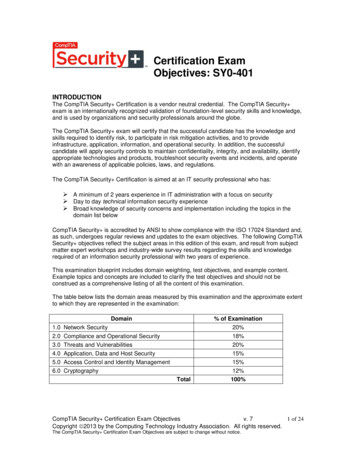
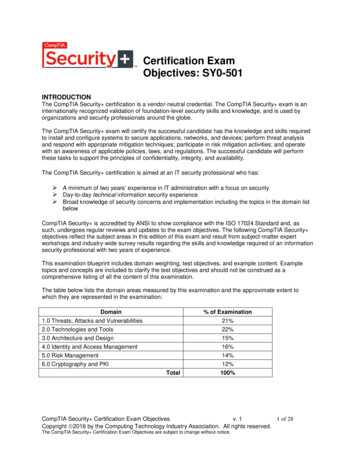
CASP- Success GuideIntroduction to CAS-002 Exam on CompTIAAdvanced Security PractitionerUse this quick start guide to collect all the information about CompTIA CASP (CAS-002)Certification exam. This study guide provides a list of objectives and resources that willhelp you prepare for items on the CAS-002 Advanced Security Practitioner exam. TheSample Questions will help you identify the type and difficulty level of the questions andthe Practice Exams will make you familiar with the format and environment of an exam.You should refer this guide carefully before attempting your actual CompTIA CASPcertification exam.The CompTIA CASP certification is mainly targeted to those candidates who want to buildtheir career in IT Security domain. The CompTIA Advanced Security Practitioner (CASP)exam verifies that the candidate possesses the fundamental knowledge and proven skillsin the area of CompTIA CASP.CompTIA CAS-002 Certification Details:Exam NameCompTIA Advanced Security Practitioner (CASP)Exam CodeCAS-002Exam Price 426 (USD)Duration165 minNumber of Questions90Passing ScorePass/FailSchedule ExamCompTIA MarketplaceSample QuestionsCompTIA CASP Sample QuestionsPractice ExamCompTIA CAS-002 Certification Practice ExamCAS-002 - CompTIA Advanced Security Practitionerpg. 2
CASP- Success GuideCompTIA CAS-002 Exam Syllabus:TopicDetailsEnterprise Security 30%1. Techniques1.2.3.4.5.6.7.8.Key stretchingHashingCode signingPseudorandom number generationPerfect forward secrecyTransport encryptionData-at-rest encryptionDigital signature2. ConceptsGiven a scenario, selectappropriate cryptographicconcepts and in of trust, root of trustCryptographic applications and proper/improperimplementationsAdvanced PKI conceptsWild cardOCSP vs. CRLIssuance to entitiesUsersSystemsApplicationsKey escrowSteganographyImplications of cryptographic methods and designStreamBlockModesECBCBCCFBOFBKnown flaws/weaknessesStrength vs. performance vs. feasibility toimplement vs. interoperability3. ImplementationsCAS-002 - CompTIA Advanced Security Practitionerpg. 3
CASP- Success SSHS/MIME1. Storage type1.2.3.4.5.6.7.Virtual storageCloud storageData warehousingData archivingNASSANvSAN2. Storage protocols1. iSCSI2. FCoE3. NFS, CIFSExplain the securityimplications associated with3. Secure storage managemententerprise pshotsDeduplicationDynamic disk poolsLUN masking/mappingHBA allocationOffsite or multisite replicationEncryptionDiskBlockFileRecordPort1. Advanced network design (wired/wireless)Given a scenario, analyzenetwork and securitycomponents, concepts andarchitectures1.2.3.4.5.Remote accessVPNSSHRDPVNCCAS-002 - CompTIA Advanced Security Practitionerpg. 4
CASP- Success GuideTopicDetails6. SSL7. IPv6 and associated transitional technologies8. Transport encryption9. Network authentication methods10. 802.1x11. Mesh networks2. Security ESIEMHSMPlacement of devicesApplication and protocol aware technologiesWAFNextGen firewallsIPSPassive vulnerability scannersDAM3. Virtual networking and security components1.2.3.4.5.SwitchesFirewallsWireless controllersRoutersProxies4. Complex network security solutions for data flow1. SSL inspection2. Network flow data5. Secure configuration and baselining of networking andsecurity components1.2.3.4.ACLsChange monitoringConfiguration lockdownAvailability controls6. Software-defined networking7. Cloud-managed networks8. Network management and monitoring toolsCAS-002 - CompTIA Advanced Security Practitionerpg. 5
CASP- Success GuideTopicDetails9. Advanced configuration of routers, switches and othernetwork devices1. Transport security2. Trunking security3. Route protection10. Security zones1. Data flow enforcement2. DMZ3. Separation of critical assets11. Network access control1. Quarantine/remediation12. Operational and consumer network-enabled devices1.2.3.4.5.6.7.Building automation systemsIP videoHVAC controllersSensorsPhysical access control systemsA/V systemsScientific/industrial equipment13. Critical infrastructure/Supervisory Control and DataAcquisition (SCADA)/ Industrial Control Systems (ICS)1. Trusted OS (e.g., how and when to use it)2. Endpoint security softwareGiven a scenario, select andtroubleshoot securitycontrols for spywareSpam filtersPatch managementHIPS/HIDSData loss preventionHost-based firewallsLog monitoring3. Host hardening1. Standard operating environment/2. configuration baselining3. Application whitelisting and blacklistingCAS-002 - CompTIA Advanced Security Practitionerpg. 6
CASP- Success GuideTopicDetails4. Security/group policy implementation5. Command shell restrictions6. Patch management7. Configuring dedicated interfaces8. Out-of-band NICs9. ACLs10. Management interface11. Data interface12. Peripheral restrictions13. USB14. Bluetooth15. Firewire16. Full disk encryption4. Security advantages and disadvantages of virtualizingservers1. Type I2. Type II3. Container-based5. Cloud augmented security services1.2.3.4.5.6.Hash matchingAntivirusAnti-spamVulnerability scanningSandboxingContent filtering6. Boot loader protections1.2.3.4.5.Secure bootMeasured launchIntegrity MeasurementArchitecture (IMA)BIOS/UEFI7. Vulnerabilities associated with co-mingling of hosts withdifferent security requirements1.2.3.4.VM escapePrivilege elevationLive VM migrationData remnants8. Virtual Desktop Infrastructure (VDI)9. Terminal services/application delivery servicesCAS-002 - CompTIA Advanced Security Practitionerpg. 7
CASP- Success GuideTopicDetails10. TPM11. VTPM12. HSM1. Web application security design considerations1. Secure: by design, by default, by deployment2. Specific application .19.Differentiate applicationvulnerabilities and selectappropriate securitycontrols.Cross-Site Request Forgery (CSRF)Click-jackingSession managementInput validationSQL injectionImproper error and exception handlingPrivilege escalationImproper storage of sensitive dataFuzzing/fault injectionSecure cookie storage and transmissionBuffer overflowMemory leaksInteger overflowsRace conditionsTime of checkTime of useResource exhaustionGeo-taggingData remnants3. Application sandboxing4. Application security frameworks1. Standard libraries2. Industry-accepted approaches3. Web services security (WS-security)5.6.7.8.Secure coding standardsDatabase Activity Monitor (DAM)Web Application Firewalls (WAF)Client-side processing vs.server-side processing1.2.3.4.5.6.7.JSON/RESTBrowser extensionsActiveXJava AppletsFlashHTML5AJAXCAS-002 - CompTIA Advanced Security Practitionerpg. 8
CASP- Success GuideTopicDetails8. SOAP9. State management10. JavaScriptRisk Management and Incident Response 20%1. Risk management of new products, new technologiesand user behaviors2. New or changing business oudMerger and demerger/divestiture3. Security concerns of integrating diverse industries1.2.3.4.Interpret business andindustry influences andexplain associated securityrisks.RulesPoliciesRegulationsGeography4. Ensuring third-party providers have requisite levels ofinformation security5. Internal and external influences1.2.3.4.5.6.CompetitorsAuditors/audit findingsRegulatory entitiesInternal and externalclient requirementsTop level management6. Impact of de-perimeterization (e.g., constantlychanging network boundary)1.2.3.4.Given a scenario, executerisk mitigation planning,strategies and controls.TelecommutingCloudBYODOutsourcing1. Classify information types into levels of CIA based onorganization/industry2. Incorporate stakeholder input into CIA decisions3. Implement technical controls based on CIArequirements and policies of the organization4. Determine aggregate score of CIA5. Extreme scenario planning/worst case scenarioCAS-002 - CompTIA Advanced Security Practitionerpg. 9
CASP- Success GuideTopicDetails6. Determine minimum required security controls basedon aggregate score7. Conduct system specific risk analysis8. Make risk determination1.2.3.4.5.6.7.8.9.10.Magnitude of impactALESLELikelihood of threatMotivationSourceAROTrend analysisReturn On Investment (ROI)Total cost of ownership9. Recommend which strategy should be applied basedon risk appetite1.2.3.4.AvoidTransferMitigateAccept10. Risk management ual11. Enterprise security architecture frameworks12. Continuous improvement/monitoring13. Business continuity planning14. IT governance1. Policy development and updates in light of newbusiness, technology, risks and environment changes2. Process/procedure development and updates in light ofpolicy, environment and business changes3. Support legal compliance and advocacy by partneringCompare and contrastwith HR, legal, management and other entitiessecurity, privacy policies and4. Use common business documents to support securityprocedures based onorganizational requirements.1. Risk assessment (RA)/2. Statement Of Applicability (SOA)3. Business Impact Analysis (BIA)4. Interoperability Agreement (IA)5. Interconnection SecurityCAS-002 - CompTIA Advanced Security Practitionerpg. 10
CASP- Success GuideTopicDetails6. Agreement (ISA)7. Memorandum Of Understanding (MOU)8. Service Level Agreement (SLA)9. Operating Level Agreement (OLA)10. Non-Disclosure Agreement (NDA)11. Business Partnership Agreement (BPA)5. Use general privacy principles for sensitive information(PII)6. Support the development of policies that contain1.2.3.4.5.6.7.8.9.10.11.Separation of dutiesJob rotationMandatory vacationLeast privilegeIncident responseForensic tasksEmployment andtermination proceduresContinuous monitoringTraining and awareness for usersAuditing requirements and frequency1. E-discovery1.2.3.4.5.6.Electronic inventory and asset controlData retention policiesData recovery and storageData ownershipData handlingLegal holds2. Data breachGiven a scenario, conductincident response andrecovery procedures.1.2.3.4.5.6.7.8.Detection and collectionData itutionResponseDisclosure3. Design systems to facilitate incident response1. Internal and external violations2. Privacy policy violations3. Criminal actionsCAS-002 - CompTIA Advanced Security Practitionerpg. 11
CASP- Success GuideTopicDetails4. Insider threat5. Non-malicious threats/misconfigurations6. Establish and review system, audit and securitylogs4. Incident and emergency response1.2.3.4.Chain of custodyForensic analysis of compromised systemContinuity Of Operation Plan (COOP)Order of volatilityResearch and Analysis 18%1. Perform ongoing research1.2.3.4.Best practicesNew technologiesNew security systems and servicesTechnology evolution (e.g., RFCs, ISO)2. Situational awareness1.2.3.4.Latest client-side attacksKnowledge of current vulnerabilities and threatsZero-day mitigating controls and remediationEmergent threats and issues3. Research security implications of new business toolsApply research methods todetermine industrytrends and impact to theenterprise.1. Social media/networking2. End user cloud storage3. Integration within the business4. Global IA industry/community1.2.3.4.Computer Emergency Response Team (CERT)Conventions/conferencesThreat actorsEmerging threat sources/ threat intelligence5. Research security requirements for contracts1.2.3.4.Request For Proposal (RFP)Request For Quote (RFQ)Request For Information (RFI)AgreementsCAS-002 - CompTIA Advanced Security Practitionerpg. 12
CASP- Success GuideTopicDetails1. Create benchmarks and compare to baselines2. Prototype and test multiple solutions3. Cost benefit analysis1. ROI2. TCO4. Metrics collection and analysis5. Analyze and interpret trend data to anticipate cyberdefense needs6. Review effectiveness of existing security controls7. Reverse engineer/deconstruct existing solutions8. Analyze security solution attributes to ensure theyAnalyze scenarios to securemeet business needsthe tyRecoverability9. Conduct a lessons-learned/after-action report10. Use judgment to solve difficult problems that do nothave a best solution1. Tool typeGiven a scenario, selectmethods or tools appropriateto conduct an assessmentand analyze resultsPort scannersVulnerability scannersProtocol analyzerNetwork enumeratorPassword crackerFuzzerHTTP interceptorExploitation tools/frameworksPassive reconnaissance and intelligence gatheringtools10. Social media11. Whois12. Routing tables1.2.3.4.5.6.7.8.9.2. Methods1. Vulnerability assessment2. Malware sandboxing3. Memory dumping, runtime debuggingCAS-002 - CompTIA Advanced Security Practitionerpg. 13
CASP- Success GuideTopicDetails4. Penetration testing5. Black box6. White box7. Grey box8. Reconnaissance9. Fingerprinting10. Code review11. Social engineeringIntegration of Computing, Communications and Business Disciplines 16%1. Interpreting security requirements and goals tocommunicate with stakeholders from other disciplinesGiven a scenario, facilitatecollaboration across diversebusiness units to achievesecurity goals.1.2.3.4.5.6.7.8.9.10.Sales staffProgrammerDatabase administratorNetwork administratorManagement/executive managementFinancialHuman resourcesEmergency response teamFacilities managerPhysical security manager2. Provide objective guidance and impartialrecommendations to staff and senior management onsecurity processes and controls3. Establish effective collaboration within teams toimplement secure solutions4. IT governance1. Security of unified collaboration toolsGiven a scenario, select theappropriate control to securecommunications andcollaboration solutions.1.2.3.4.5.6.7.8.9.10.11.12.Web conferencingVideo conferencingInstant messagingDesktop sharingRemote assistancePresenceEmailTelephonyVoIPCollaboration sitesSocial mediaCloud-based2. Remote access3. Mobile device managementCAS-002 - CompTIA Advanced Security Practitionerpg. 14
CASP- Success GuideTopicDetails1. BYOD4. Over-the-air technologies concerns1. End-to-end solution ownership1.2.3.4.5.6.Operational Asset disposalAsset/object reuseGeneral change management2. Systems development life cycle1. Security System DevelopmentLife CycleImplement security activitiesacross the technology lifecycle.(SSDLC)/Security Development Lifecycle (SDL)2. Security Requirements Traceability Matrix (SRTM)3. Validation and acceptance testing4. Security implications of agile, waterfall and spiralsoftware development methodologies3. Adapt solutions to address emerging threats andsecurity trends4. Asset management (inventory control)1.2.3.4.5.Device tracking technologiesGeo-location/GPS locationObject tracking and containment technologiesGeo-tagging/geo-fencingRFIDTechnical Integration of Enterprise Components 16%1. Secure data flows to meet changing business needs2. StandardsGiven a scenario, integratehosts, storage, networks andapplications into a secureenterprise architecture.1.2.3.4.5.Open standardsAdherence to standardsCompeting standardsLack of standardsDe facto standards3. Interoperability issues1. Legacy systems/current systems2. Application requirementsCAS-002 - CompTIA Advanced Security Practitionerpg. 15
CASP- Success GuideTopicDetails3. In-house developed vs. commercial vs. commercialcustomized4. Technical deployment models(outsourcing/insourcing/managed services/partnership)1. Cloud and virtualization considerations and 19.20.21.optionsPublicPrivate HybridCommunityMulti-tenancySingle tenancyVulnerabilities associated with a single physicalserver hosting multiple companies’ virtualmachinesVulnerabilities associated with a single platformhosting multiple companies’ virtual machinesSecure use of on-demand/ elastic cloud computingData remnantsData aggregationData isolationResources provisioning and deprovisioningUsersServersVirtual devicesApplicationsSecuring virtual environments, services,applications, appliances and equipmentDesign considerations during mergers, acquisitionsand demergers/divestituresNetwork secure segmentation and delegation5. Logical deployment diagram and corresponding physicaldeployment diagram of all relevant devices6. Secure infrastructure design (e.g., decide where toplace certain devices/applications)7. Storage integration (security considerations)8. Enterprise application integration enablers1.2.3.4.5.6.7.CRMERPGRCESBSOADirectory servicesDNSCAS-002 - CompTIA Advanced Security Practitionerpg. 16
CASP- Success GuideTopicDetails8. CMDB9. CMS1. Authentication1. Certificate-based authentication2. Single sign-on2. Authorization1. OAUTH2. XACML3. SPMLGiven a scenario, integrate3. Attestationadvanced authentication and4. Identity propagationauthorization technologies to5. Federationsupport enterpriseobjectives.1. SAML2. OpenID3. Shibboleth4. WAYF6. Advanced trust models1. RADIUS configurations2. LDAP3. ADCAS-002 Sample Questions:01. A new system has recently been built using the SSDLC process and is inthe validation process to ensure the system is behaving correctly. During thisprocess, the development team notices that the system is behaving as itshould, except for a few minor internal application bugs. Which of thefollowing validation types would be a result of this issue?a) Application interface validationb) Code validationc) Functional validationd) Requirements validationCAS-002 - CompTIA Advanced Security Practitionerpg. 17
CASP- Success Guide02. A server administrator needs to find a web service that will allow mostsystems to communicate over HTTP using an XML based protocol. Which of thefollowing communication methods will allow this?a) SOAPb) XACMLc) SSOd) SAML03. When considering security requirements which require third party vendorrequests, which of the following is a correctly ordered set of events from startto finish?a) RFP, RFQ, RFCb) RFI, RFQ, RFPc) RFP, RFQ, RFId) RFC, RFT04. As a condition of being awarded a new contract, an organization mustincrease the security of its VPN ensuring that one compromised SA session keycannot be used to compromise any other sessions. Which of the followingcould be configured to meet this requirement?a) Opportunistic encryptionb) Pseudo-random number generatorc) Dual-factor authenticationd) Perfect forward secrecy05. During a routine security assessment of a network, the securityadministrator discovers a user workstation with multiple SSH connections toservers outside the corporate network. Using a protocol analyzer, theadministrator identifies hundreds of gigabytes of information beingtransferred to an external server via SCP.After identifying the user, the administrator discovers that today is the user’slast day of employment, and that the employee is going to work for acompetitor. Which of the following tactics is being used to steal companysecrets?a) Logic bombb) SSH wormc) Data exfiltrationd) Privilege escalatione) SAML exploit06. Which of the following practices is MOST likely employed during ediscovery?a) Legal hold and chain of custodyb) Risk mitigation and policy generationc) Network enumeration and fingerprintingd) Data deduplication and hashingCAS-002 - CompTIA Advanced Security Practitionerpg. 18
CASP- Success Guide07. A security administrator notices a network intrusion and quickly solves theproblem by closing an unused port. Which of the following should becompleted?a) After action reportb) ELAc) MOAd) Reverse engineering incident report08. An IT Manager has requested that specific files stored on the company SANcontaining data which is not protected by patent law, but is classified as tradesecret encrypted with a block cipher which is both secure and fast. Which ofthe following BEST satisfies the request?a) Blowfishb) MD5c) Triple-DESd) RC409. A new Chief Information Officer’s (CIO’s) primary initiative is to reducerisk and the number of vulnerabilities affecting an organization. Which of thefollowing reduces the number of locations to patch internal applications?a) Provide application access through a VDIb) Host applications using terminal servicesc) Implement an enterprise patch management solutiond) Convert applications to leverage hosted cloud computing10. An administrator uses an iSCSI unencrypted connection over the corporatenetwork. Which of the following vulnerabilities would be present in regards toiSCSI authentication?a) Authentication uses the older TACACS protocol and is vulnerable to a botnet attack.b) Authentication is vulnerable to a dictionary attack.c) iSCSI uses LDAP authentication in plain text, which can be easily compromised.d) Kerberos authentication would not be supported on Linux hosts.Answers to CAS-002 Exam Questions:Question: 01Answer: bQuestion: 02Answer: aQuestion: 03Answer: bQuestion: 04Answer: dQuestion: 05Answer: cQuestion: 06Answer: aQuestion: 07Answer: aQuestion: 08Answer: aQuestion: 09Answer: bQuestion: 10Answer: bNote: If you find any typo or data entry error in these sample questions, we requestyou to update us by commenting on this page or write an email onfeedback@edusum.comCAS-002 - CompTIA Advanced Security Practitionerpg. 19
The CompTIA CASP certification is mainly targeted to those candidates who want to build their career in IT Security domain. The CompTIA Advanced Security Practitioner (CASP) exam verifies that the candidate possesses the fundamental knowledge and proven skills in the area of CompTIA CASP. CompTIA CAS-002 Cert